All-in-one protection for Microsoft 365
All-in-one protection for Microsoft 365

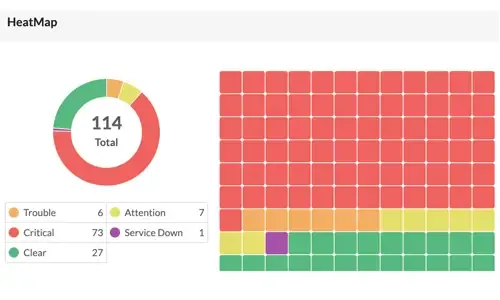
OpManager: Network & DC Monitoring
Monitor & Manage Network, Datacenters, endpoints & more.
Free NDIS2 Compliance Webinar
- Compliance & Cybersecurity
- NIS2 & GDPR overlap
Latest Articles
Unlock Deep Visibility & Insight into Windows Server 2022 Logs
 This article explores the exciting new features of Windows Server 2022 and emphasizes the critical role of analyzing Windows Server logs. You'll also discover how EventLog Analyzer provides comprehensive, helps you achieve 360-degree protection against threats targeting these logs, ensuring robust security for your server environment.
This article explores the exciting new features of Windows Server 2022 and emphasizes the critical role of analyzing Windows Server logs. You'll also discover how EventLog Analyzer provides comprehensive, helps you achieve 360-degree protection against threats targeting these logs, ensuring robust security for your server environment.
Key Topics:
- The Importance of Proactive Log Management
- Windows Server 2022 and its Key Features
- Understanding Windows Server Logs
- The Importance of Analyzing Windows Server Logs
- Benefits of Using EventLog Analyzer for Windows Server Log Analysis
- Configuring EventLog Analyzer to Connect to Windows Server
- Summary
Download your copy of EventLog Analyzer
Related Articles:
- Event Log Monitoring System: Implementation, Challenges & Standards Compliance
- Detecting Windows Server Security Threats with Advanced Event Log Analyzers
The Importance of Proactive Log Management
Did you know that threats targeting Windows Server and its logs are becoming more significant? To protect your systems, you must monitor and analyze these logs effectively. Ensuring system security, compliance, and health requires effective log management.
Administrators can ensure optimal performance by promptly identifying and resolving issues through routine log review. Log analysis also protects sensitive data by assisting in the detection of any security breaches and unwanted access. Proactive log management ultimately improves the security and dependability of the IT infrastructure as a whole.
EventLog Analyzer monitors various Windows event logs, such as security audit, account management, system, and policy change event logs. The insights gleaned from these logs are displayed in the forms of comprehensive reports and user-friendly dashboards to facilitate the proactive resolution of security issues.
Windows Server 2022 and its Key Features
Windows Server 2022 is a server operating system developed by Microsoft as a part of the Windows New Technology family. It is the most recent version of the Windows Server operating system, having been released in August 2021. Large-scale IT infrastructures can benefit from the enterprise-level administration, storage, and security features offered by Windows Server 2022. Compared to its predecessors, it has various new and improved capabilities, with an emphasis on application platform advancements, security, and hybrid cloud integrations.
Let’s take a look at a few key features of Windows Server 2022:
- Cutting-edge security features, such as firmware protection, virtualization-based security, hardware roots of trust, and secured-core servers, that protect against complex attacks.
- Improved management and integrations with Azure services via Azure Arc's support for hybrid cloud environments.
- New storage features, which include Storage Migration Service enhancements, support for larger clusters, and improvements to Storage Spaces Direct.
- Enhancements to Kubernetes, container performance, and Windows containers in Azure Kubernetes Service to improve support for containerized applications.
- Support for more powerful hardware configurations, including more memory and CPU capacity, with enhanced performance for virtualized workloads.
- File size reductions during transfers to increase efficiency and speed through the use of Server Message Block (SMB) compression.
- An integration with Azure Automanage for easier deployment, management, and monitoring of servers in hybrid and on-premises environments.
- Improved networking features, such as enhanced network security and performance as well as support for DNS over HTTPS.
- Enhanced VPN and hybrid connectivity options, such as an SMB over QUIC capability that permits safe, low-latency file sharing over the internet.
- Improvements to Windows Subsystem for Linux and tighter integration for cross-platform management, which provides better support for executing Linux workloads.
- A range of flexible deployment and licensing options, such as the usage of Azure's subscription-based licensing.
- Support for modernizing existing .NET applications and developing new applications using the latest .NET 5.0 technologies.
- Enhanced automation capabilities with the latest version of PowerShell, PowerShell 7.
Understanding Windows Server Logs
Windows Server event logs are records of events that occur within the operating system or other software running on a Windows server. You can manage, observe, and troubleshoot the server environment with the help of these logs. The logs capture numerous pieces of information, such as application problems, security incidents, and system events. By examining and evaluating these logs, administrators can ensure the security, functionality, and health of the server.
Ultimate Guide: Install Windows 11 on VMware ESXi – Easily Bypass TPM Security Requirement
 In this article, we’ll show you how to setup or install Microsoft Windows 11 on VMware’s ESXi servers and bypass the Trusted Platform Module version 2.0 (TPM 2.0) requirement. We've also made the TPM bypass ISO image available as a free download.
In this article, we’ll show you how to setup or install Microsoft Windows 11 on VMware’s ESXi servers and bypass the Trusted Platform Module version 2.0 (TPM 2.0) requirement. We've also made the TPM bypass ISO image available as a free download.
Key Topics:
Download now your free copy of the latest V9 VM backup now.
VMware ESXi – TPM – vTPM and Windows 11
Trusted Platform Module version 2.0 (TPM 2.0) is required to run Microsoft’s Windows 11. This restricts the operating system’s installation on newer PCs, it also means users with older hardware are likely to be forced to upgrade. While the virtualization world is often more forgiving when it comes to hardware requirements, trying to install Windows 11 on VMware’s ESXi platform usually present the error: “This PC can’t run Windows 11”:
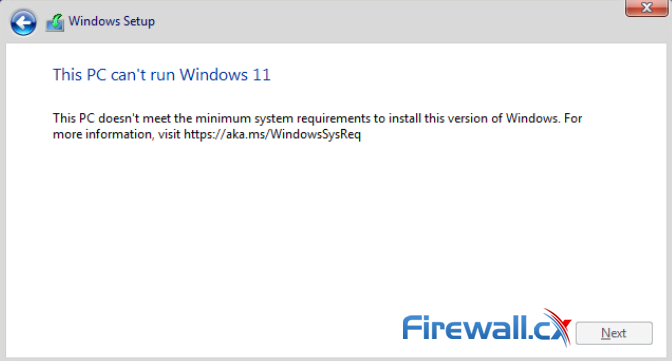 Windows 11 Installation Error in VMware ESXi
Windows 11 Installation Error in VMware ESXi
Running Windows 11 as a virtual machine on VMware ESXi requires a virtual Trusted Platform Module (vTPM) present. For more details on Microsoft Windows 11 requirements see, https://docs.microsoft.com/en-us/windows/whats-new/windows-11-requirements.
While VMware supports vTPM and doesn’t require a physical TPM 2.0 chip, to use it, you need to configure a number of different services, depending on your VMware Platform version, including vCenter, vSphere Native Key Provider and more, making it a complicated task – especially for those running home labs. For more details see, https://core.vmware.com/resource/windows-11-support-vsphere#section2.
The next steps will take you through downloading the TPM ISO image used to bypass the Windows TPM check.
Elevate your network management: Maximizing efficiency with ManageEngine Network Configuration Manager
 As technology evolves, so do our networks. Today's sprawling network infrastructures are intricate ecosystems, demanding more from IT teams than ever before. Configuration management, compliance enforcement, and firmware & software updates are just a few of the growing requirements that strain manual processes.
As technology evolves, so do our networks. Today's sprawling network infrastructures are intricate ecosystems, demanding more from IT teams than ever before. Configuration management, compliance enforcement, and firmware & software updates are just a few of the growing requirements that strain manual processes.
While manual network management might have sufficed in simpler times, it hinders scalability in complex environments. It can also introduce security vulnerabilities and leave your network prone to human error.
To navigate this new reality, organizations need a better approach—they need to leverage a network configuration management tool.
Now, let's explore how a network configuration management tool can help revolutionize your modern network, unlocking a new era of scalability and security.
Key Topics:
- Manual Configuration Challenges: Leveraging Configuration Management Tools
- Scalability Hurdles
- Backup Maintenance
- Configuration Tracking
- Firmware Vulnerability Management
- Adherence to Compliance Standards
- Streamlining Mundane Tasks
- Report Maintenance
- Selecting the Right Configuration Management Tool for your Network
- Vendor Versatility
- Backups
- Change Management
- Compliance Management
- Vulnerability Management
- Automation
- Reporting
- Device Onboarding
- Network Configuration Manager: Your All-In-One Configuration Management Tool
- Summary
Related articles:
- Maximizing Network Security: A Deep Dive into OpManager's Firewall Analyzer Add-on
- Boost Network Security and Efficiency with Intelligent Notifications and Automated Fault Handling. Unified IT Operations Management Tool
- Ensuring Compliance and Business Continuity in a Hybrid Work Environment
- Dealing with Security Audit Challenges: Discovering vulnerabilities, unauthorized access, optimize network security & reporting
Manual Configuration Management Challenges: Why a Configuration Management Tool is a Game-Changer
Complete Guide: How to Download & Deploy The Cisco 9800-CL Virtual Wireless Controller on VMware ESXi
 This article covers the deployment of the Cisco WLC 9800-CL cloud-based controller on the VMware ESXi platform. We explain the CPU, RAM and storage requirements, provide URLs to easily download and install the WLC controller using the OVA template, select the appropriate WLC 9800 deployment size (small, medium, large) and help you understand and configure the different WLC VM network interfaces.
This article covers the deployment of the Cisco WLC 9800-CL cloud-based controller on the VMware ESXi platform. We explain the CPU, RAM and storage requirements, provide URLs to easily download and install the WLC controller using the OVA template, select the appropriate WLC 9800 deployment size (small, medium, large) and help you understand and configure the different WLC VM network interfaces.
Key Topics:
- Introduction to the Cisco 9800 WLC Virtual Controller
- Cisco 9800 WLC Virtual Controller VMware ESXi Requirements
- Cisco 9800 WLC Virtual Controller Deployment Models
- How to Download the Cisco 9800-CL Software
- Installing the Cisco 9800 WLC Virtual Controller in VMware ESXi
- Critical VMware Network Information on the Cisco 9800-CL – vNICs, vSwitch etc.
- Configure a VMware Port Group to Allow Trunking or Single VLAN
- Summary
Introduction to the Cisco 9800 WLC Virtual Controller
Cisco released their next-generation 9800 series Wireless Controllers back in 2018, also offering a cloud-based version that supports VMware ESXi, Microsoft Hyper-V, Amazon AWS, Microsoft Azure, Google Cloud Platform (GCP), Ubuntu/Red Hat Enterprise Linux using KVM, and Cisco NFVIS environments.
The virtualized version of the WLC controller offers great flexibility for organizations while at the same time provides considerable savings thanks to its zero-price tag. Customers are able to freely download and deploy the appliance, with the only restriction being the AP licenses that need to be purchased as an ongoing subscription.
Virtualization offers additional benefits which include:
- Hardware independence. Not hardware involved. Lead times for the hardware-based controllers can sometimes exceed 6-9 months depending on the market demand and other circumstances.
- Decreased cost. The VM option means organizations are saving 6-figure amounts for every 9800-40 or greater model they require. If you’re considering introducing High-Availability (HA), then the Cloud-based controller becomes a much cheaper architecture. Additional savings are added since Smartnet contracts for the hardware are not required.
- Better utilization of virtualization infrastructure. Utilizing the existing virtualization platform increases its ROI.
- Greater Deployment Flexibility. VMs allow you to easily move them from one physical server to another, even between different datacenters or physical locations.
- Increased Redundancy & Backups. Backing up a VM is an easy and simple process. You can even use specialized free VM Backup tools for this process.
Cisco 9800 WLC Virtual Controller VMware ESXi Requirements
Deploying the WLC 9800-CL in an ESXi environment is, as you’ll discover, a simple process. Cisco provides a single OVA file package, roughly around 1.25GB in size:
Your IP address:
18.117.170.226
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Featured Categories:
Top Picks:

Dealing with Security Audit Challenges: Discove...
Complete Guide to Upgrading Palo Alto Firewall ...
Boost Network Security and Efficiency with Inte...
Palo Alto Firewalls Security Zones – Tap Zone, ...
Complete Guide to SD-WAN. Technology Benefits, SD-WAN Security, Management, Mobility, VPNs, Architecture & Comparison with Traditional WANs. SD-WAN Providers Feature Checklist.
How To Secure Your SD-WAN. Comparing DIY, Managed SD-WAN and SD-WAN Cloud Services
Security Service Edge (SSE) Limitations & Disadvantages. Protecting all Traffic, Users, Apps, and Services with 360-degree SSE
Configuring A SASE Unified Network: Data centers, Remote Sites, VPN Users, and more

Comparing Traditional Flat & VLAN Networks

VLAN InterSwitch Link (ISL) Protocol Analysis

Static VLANs

InterVLAN Routing - Routing between VLAN Networks
Link State Routing Protocols
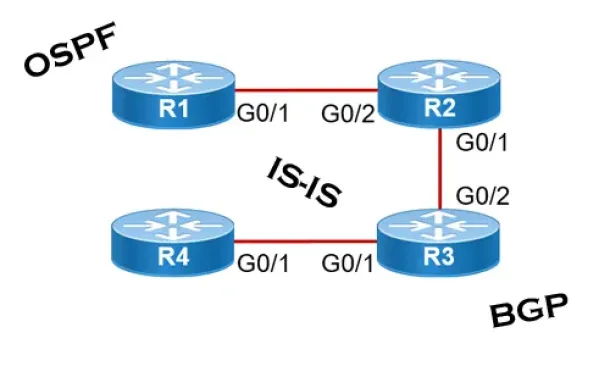
Routed Protocols
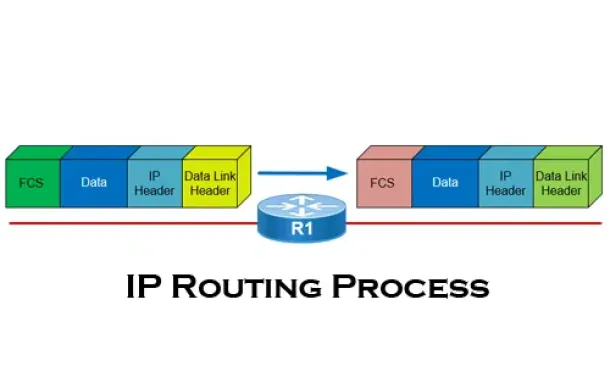
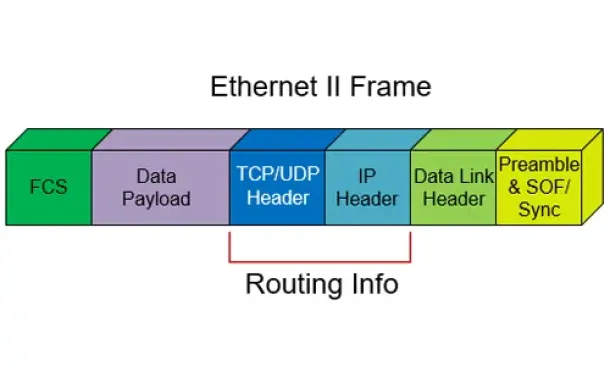
The IP Routing Process - Step-by-Step Analysis