Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
|
Articles:
The OSI Model: Layer 5 - Session Layer
| Read |
|
Articles:
The OSI Model: Layer 4 - Transport Layer
| Read |
|
Articles:
The OSI Model: Layer 3 - Network Layer
| Read |
|
Articles:
The OSI Model: Layer 2 - Datalink Layer
| Read |
|
Articles:
The OSI Model: Layer 1 - Physical Layer
| Read |
Suggested Articles:
Network Fundamentals
Power over Ethernet - Understanding PoE Technolog…
Power over Ethernet (PoE) was invented by PowerDsine back in 1997 and the first power injector (Midspan) was installed in 1998! Many manufacturespart…
Ethernet Protocol, CSMA/CD, Collisions
Integrating Fast Ethernet into 10MB Ethernet Netw…
Now that Fast Ethernet is here, the question becomes, "How do I start using it ?" Integrating Fast Ethernet into existing networks need not be done a…
Ethernet Protocol, CSMA/CD, Collisions
802.3 Fast Ethernet (100 Mbit/Sec) Model
Here we see a logical drawing of the Fast Ethernet Data Link Layer sublayers. Data is passed down from the upper layers (such as TCP/IP or Novell Net…
Network Address Translation - NAT
The Network Address Translation Table
After that simple and informative introduction to the NAT concept, it's time to find out more about how it works and this is where the NAT table come…
Featured Subcategories:
Netflow Articles:

NetFlow Analyzer: Free Download, Step-by-Step Ins…
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows w…

Netflow: Monitor Bandwidth & Network Utilization…
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, applic…

Bandwidth Detective: Uncover Hidden Traffic and E…
In this article, we explore the core principles of bandwidth management and examine how modern network monitoring technologies can assist in maintain…

Netflow vs SNMP. Two Different Approaches to Netw…
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ne…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!

VLAN Networks
VTP Pruning
VTP (VLAN Trunking Protocol) pruning is a feature that is used in Cisco switches to reduce unnecessary traffic in VLAN (Virtual Local Area Network) trunks…

VLAN Networks
Static VLANs
VLANs are usually created by the network administrator, assigning each port of every switch to a VLAN. Depending on the network infrastructure and securit…

VLAN Networks
InterVLAN Routing - Routing between VLAN Networks
This article deals with the popular topic of InterVLAN routing, which is used to allow routing & communication between VLAN networks. Our article anal…

VLAN Networks
VLANs - Access & Trunk Links
If you've read our previous article The VLAN Concept - Introduction to VLANs then you should feel comfortable with terms such as 'VLAN', 'Stati…
Routing
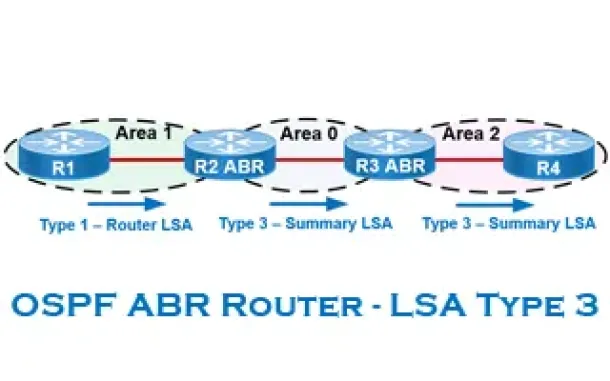
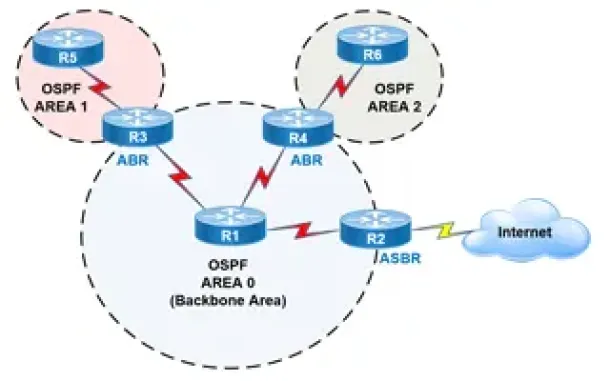
OSPF - Part 6: OSPF LSA Types - Purpose and Function o…
Our previous article explained the purpose of Link State Update (LSU) packets and examined the Link State Advertisement (LSA) information contained within…
Routing
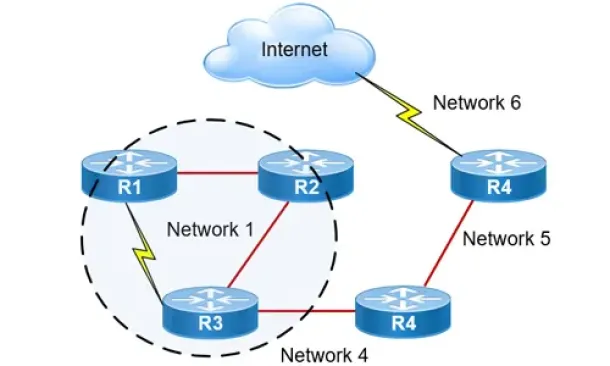
OSPF - Part 2: How OSPF Protocol Works & Basic Concept…
This article covers basic OSPF concepts and operation. We explain how OSPF works, how OSPF tables are built on an OSPF-enabled router and their purpose (N…
Routing
Hybrid Routing Protocols - Advantages and Disadvantage…
Hybrid routing protocols are a combination of distance-vector and link-state routing protocols, and are used to provide a more efficient and scalabl…
Routing
Routed Protocols
We all understand that TCP/IP, IPX-SPX are protocols which are used in a Local Area Network (LAN) so computers can communicate between with each other and…
Windows Servers
Installation and Configuration of Fine-Grained Passwor…
Microsoft introduced Fine-Grained Password Policy for the first time in Windows Server 2008 and the policy has been part of every Windows Server since the…
Windows Servers
How to Install and Configure SNMP for Windows Server 2…
Simple Network Management Protocol (SNMP) is a UDP protocol that uses port 161 to monitor and collect detailed information on any network device supportin…
SASE & SD-WAN Networks
Check Point Software and Cato Networks Co-Founder Shlo…
By: Shlomo Kramer, Check Point Software & Cato Networks Co-Founder
As one of the founders of Check Point Software and more recently Cato Networks, I’…
Cisco Routers
MPLS Case Study: Why Route Summarization is not Recomm…
MPLS generates Implicit Null label (The Implicit NULL label is the label that has a value of 3) for directly connected interfaces and for the summary rout…

















