Network Management Articles:

OpManager - Network Monitoring & Management
Maximizing Network Security: A Deep Dive into OpM…
In the rapidly evolving landscape of cyber threats, network security has never been more crucial. With the frequency and sophistication of cyberattacks escalating, organizations are under constant pr…
OpManager - Network Monitoring & Management
Ensuring Enterprise Network Readiness for Mobile…
Demands for Enterprise networks to properly support mobile users is on a continuous rise making it more than ever necessary for IT departments to provide high-quality services to its users. This arti…

Netflow
Netflow: Monitor Bandwidth & Network Utilization…
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, application traffic and data flows allows network engine…

ManageEngine Firewall Analyzer
Achieving Modern Compliance: Navigate PCI DSS v4…
In an era where cyber threats are growing in both volume and sophistication, failing to meet security compliance standards is no longer just a legal issue—it’s a business risk with potentially catast…
Featured Subcategories:
Network Protocol Analyzer Articles:
Network Protocol Analyzers
How to Detect SYN Flood Attacks with Capsa Networ…
This article explains how to detect a SYN Flood Attack using an advanced protocol analyser like Colasoft Capsa. We’ll show you how to identify and inspect abnormal traffic spikes, drill into captured…
Network Protocol Analyzers
Introducing Colasoft Unified Performance Manageme…
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, quality, fault, and security issues based on business…
Network Protocol Analyzers
How to Perform TCP SYN Flood DoS Attack & Detect…
This article will help you understand TCP SYN Flood Attacks, show how to perform a SYN Flood Attack (DoS attack) using Kali Linux & hping3 and correctly identify one using the Wireshark protocol…
Network Protocol Analyzers
How to Reconstruct HTTP Packets/Data & Monitor HT…
HTTP reconstruction is an advanced network security feature offered by nChronos version 4.3.0 and later. nChronos is a Network Forensic Analysis application that captures packets/data around the cloc…
Virtualization & VM Backup:
Virtualization & VM Backup
6 Key Areas to Consider When Selecting a VM Backu…
Backup and Disaster recovery are core considerations for any business with an IT footprint, whether that is on-premises or in the cloud.
Your business depends on reliable IT systems to support the b…
Virtualization & VM Backup
SysAdmin Day 2020 - Get your Free Amazon Voucher…
SysAdmin Day has arrived, and with it, gratitude for all the unsung heroes that 2020 has needed. Your hard work has made it possible for all of us to keep going, despite all challenges thrown our way…
Virtualization & VM Backup
Differences Between VMware vSphere, vCenter, ESXi…
In this article we will cover the differences between VMware ESXi, vSphere and vCenter while also explain the features supported by each vSphere edition: vSphere Standard, Enterprise plus and Plantiu…
Virtualization & VM Backup
The Backup Bible. A Free Complete Guide to Disast…
The Free Backup Bible Complete Edition written by backup expert and Microsoft MVP Eric Siron, is comprised of 200+ pages of actionable content divided into 3 core parts, including 11 customizable tem…
Firewall Articles:

Cisco Firewalls
Converting Cisco Firepower from Platform mode to…
This article explains how to configure a Cisco Firepower 2100 series device to operate in Appliance mode. We’ll show you how to switch from Platform mode to Appliance mode and how the device will aut…
Palo Alto Networks
Palo Alto Firewall Configuration Options. Tap Mod…
Our previous article explained how Palo Alto Firewalls make use of Security Zones to process and enforce security policies. This article will explain the different configuration options for physical…
Palo Alto Networks
The Benefits of Palo Alto Networks Firewall Singl…
What makes Palo Alto Networks Next-Generation Firewall (NGFW) so different from its competitors is its Platform, Process and Architecture. Palo Alto Networks delivers all the next generation firewall…
Palo Alto Networks
How to Fix Palo Alto Firewall “Error: Image File…
Keeping your Palo Alto Firewall up to date with the latest PAN-OS software updates is an important step to ensure your organization is protected against the PAN-OS latest software vulnerabilities, so…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Top Picks
Routing
Routed Protocols
We all understand that TCP/IP, IPX-SPX are protocols which are used in a Local Area Network (LAN) so computers can communicate between with each othe…
Routing
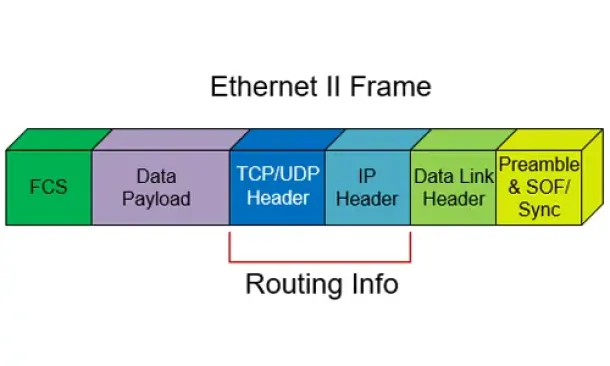
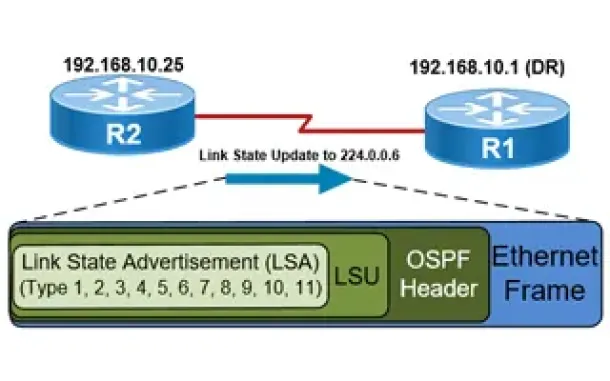
OSPF - Part 5: Analysis of OSPF Link State Update (LSU) - Link State Advertisement (LSA) Packet Structure. Common LSA Types
This article explains how OSPF uses Link State Advertisement (LSA) to exchange information about the network topology between routers. When a router…
Security Service Edge (SSE)
Security Service Edge (SSE) Limitations & Disadvantages. Protecting all Traffic, Users, Apps, and Services with 360-degree SSE
This article explores the Security Service Edge (SSE) portion of Secure Access Service Edge (SASE) and the need for holistic cybersecurity protection…
Windows Servers
Understanding, Creating, Configuring & Applying Windows Server 2012 Active Directory Group Policies
This article explains what Group Policies are and shows how to configure Windows Server 2012 Active Directory Group Policies. Our next article will c…

















