Suggested Articles:
Network Protocol Analyzers
Advanced Network Protocol Analyzer Review: Cola...
Firewall.cx has covered Colasoft Capsa several times in the past, but its constant improvements make it well worth revisiting. Since the last revie...
Network Protocol Analyzers
How To Detect ARP Attacks & ARP Flooding With C...
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC addr...

EventLog Analyzer
Detecting Windows Server Security Threats with ...
Windows Servers stand as prime targets for hackers and malicious actors due to their widespread usage and historical vulnerabilities. These systems...
Network Protocol Analyzers
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...
Featured Subcategories:
WireShark Articles:
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing proce...
How to Reconstruct HTTP Packets/Data & Monitor ...
HTTP reconstruction is an advanced network security feature offered by nChronos version 4.3.0 and later. nChronos is a Network Forensic Analysis ap...
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...
Introducing Colasoft Unified Performance Manage...
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, qua...
Your IP address:
3.135.216.20
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
How to Register a Palo Alto Firewall and Activate Su...
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product upda...
Palo Alto Networks
Introduction to Palo Alto Next-Generation Network Fi...
During the past decade, we’ve seen the global IT security market flooded with new network security and firewall security appliances. New vendors emergin...
Palo Alto Networks
Palo Alto Firewall Application-based Policy Enforcem...
Our previous article examined the benefits of Palo Alto Networks Firewall Single Pass Parallel Processing (SP3) architecture and how its combine with th...

Palo Alto Networks
Configuring QoS on Palo Alto Firewalls: Class-based ...
This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and efficient ...
Windows Servers
Simple Guide on Installing & Configuring a Windows 2...
A Windows Active Directory Certification Authority server (AD CA), also known as a Certificate Authority, is an essential service to every organization’...
Windows Servers
How to Recover & Create "Show Desktop" Icon Function...
The Show Desktop feature, included with almost all versions of Windows up to Windows 7, allows a user to minimize or restore all open programs and easi...
Windows Servers
Creating a Virtual Machine in Windows Hyper-V. Confi...
Our previous articles covered basic concepts of Virtualization along with the installation and monitoring of Windows 2012 Hyper-V. This article takes th...
Windows Servers
Installing Active Directory Services & Domain Contro...
This article serves as an Active Directory tutorial covering installation and setup of Windows 2012 Active Directory Services Role & Domain Controll...
Popular Topics
Network Fundamentals
Media Access Control - MAC Addresses
A MAC address, or Media Access Control address, is a unique identifier assigned to a network interface controller (NIC) for use as a network address i...
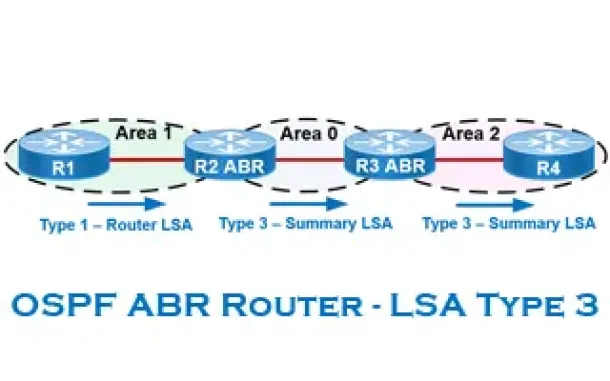
Routing
OSPF - Part 6: OSPF LSA Types - Purpose and Function...
Our previous article explained the purpose of Link State Update (LSU) packets and examined the Link State Advertisement (LSA) information contained with...
Windows Servers
Renaming Windows 2000 Domain Name
Sometimes renaming a domain is an essential business requirement. There are many situations, such as mergers, change of company name or migration from a...
Network Protocol Analyzers
Advanced Network Protocol Analyzer Review: Colasoft ...
Firewall.cx has covered Colasoft Capsa several times in the past, but its constant improvements make it well worth revisiting. Since the last review, th...
Cisco Services & Technologies
Comparing DMVPN Single Tier and Dual Tier Headend Ar...
This article extends our DMVPN article series by answering common questions regarding the differences between Single Tier Headend and Dual Tier Headend ...
Cisco Switches
How to Disable or Enable the Password Recovery Proce...
Our previous article shows how to perform a password recovery on the Cisco Catalyst switches. This article will now explain how to disable or enable the...
Cisco Routers
Enabling & Configuring SSH on Cisco Routers. Restric...
This article shows how to configure and setup SSH for remote management of Cisco IOS Routers. We’ll show you how to check if SSH is supported by your IO...
Cisco Services & Technologies
Comparing Cisco VPN Technologies – Policy Based vs R...
Virtual Private Networks constitute a hot topic in networking because they provide low cost and secure communications between sites (site-to-site VPNs) ...




















