Suggested Articles:

EventLog Analyzer
Detecting Windows Server Security Threats with ...
Windows Servers stand as prime targets for hackers and malicious actors due to their widespread usage and historical vulnerabilities. These systems...
Network Protocol Analyzers
Introducing Colasoft Unified Performance Manage...
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, qua...
OpManager - Network Monitoring & Management
Network Management Systems Help Businesses Accu...
Accurately monitoring your organization’s business application performance, service provider SLA breaches, network infrastructure traffic, bandwidt...

OpManager - Network Monitoring & Management
Maximizing Network Security: A Deep Dive into O...
In the rapidly evolving landscape of cyber threats, network security has never been more crucial. With the frequency and sophistication of cyberatt...
Featured Subcategories:
WireShark Articles:
How to Detect Routing Loops and Physical Loops ...
When working with medium to large scale networks, IT departments are often faced dealing with network loops and broadcast storms that are caused by...
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing proce...
Improve Network Analysis Efficiency with Colaso...
Troubleshooting network problems can be a very difficult and challenging task. While most IT engineers use a network analyzer to help solve network...
How to Detect SYN Flood Attacks with Capsa Netw...
This article explains how to detect a SYN Flood Attack using an advanced protocol analyser like Colasoft Capsa. We’ll show you how to identify and ...
Your IP address:
18.227.183.238
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
Palo Alto Firewalls Security Zones – Tap Zone, Virtu...
Palo Alto Networks Next-Generation Firewalls rely on the concept of security zones in order to apply security policies. This means that access lists (fi...
Palo Alto Networks
How to Register a Palo Alto Firewall and Activate Su...
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product upda...
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial Conf...
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Firew...

Palo Alto Networks
Configuring QoS on Palo Alto Firewalls: Class-based ...
This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and efficient ...
Windows Servers
Renaming Windows 2000 Domain Name
Sometimes renaming a domain is an essential business requirement. There are many situations, such as mergers, change of company name or migration from a...
Windows Servers
Hyper-V Best Practices - Replica, Cluster, Backup Ad...
Hyper-V has proven to be a very cost effective solution for server consolidation. Evidence of this is also the fact that companies are beginning to move...
Windows Servers
New Features in Windows Server 2012 - Why Upgrade t...
There is no doubt that Cloud Computing is hot topic these days. Innovations in cloud computing models have made every industry and company IT department...
Windows Servers
How to Enable & Configure Shadow Copy for Shared Fol...
When you shadow copy a disk volume, you are actually generating a snapshot of the changes made to the folders and files within the disk volume at a cert...
Popular Topics
Windows Servers
Free Webinar & eBook on Microsoft Licensing for Virt...
Microsoft Licensing for Virtual environments can become a very complicated topic, especially with all the misconceptions and false information out there...
Virtualization & VM Backup
Understanding Deduplication. Complete Guide to Dedup...
When considering your VM backup solution, key features such as deduplication are incredibly important. This is not simply from a cost perspective but al...
Network Fundamentals
Power over Ethernet - Understanding PoE Technology, ...
Power over Ethernet (PoE) was invented by PowerDsine back in 1997 and the first power injector (Midspan) was installed in 1998! Many manufacturespartner...
VLAN Networks
Dynamic VLANs
Dynamic VLANs were introduced to grant the flexibility and complexity(!) that Static VLANs did not provide. Dynamic VLANs are quite rare because of thei...
Cisco Routers
How To Secure Your Cisco Router Using Cisco AutoSecu...
In today’s complex network environments securing your network routers can be a daunting task, especially when there are so many CLI commands and paramet...
Cisco Routers
Configuring Static Route Tracking using IP SLA (Basic)
In today's network environment, redundancy is one of the most important aspects, whether its on the LAN side or on the WAN side. In this topic we will b...
Cisco Wireless
Understanding, Configuring & Tweaking Web-based Cisc...
Cisco Aironet Access Points, just like most Cisco devices, provide a web interface from which we are able to configure the device. It is often we are pr...
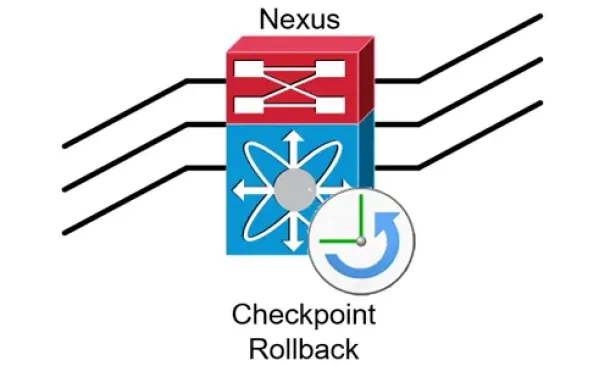
Cisco Data Center (Nexus/UCS)
Complete Guide to Nexus Checkpoint & Rollback Featur...
The Cisco NX-OS checkpoint feature provides the capability to capture at any time a snapshot (backup) of the Cisco Nexus configuration be...




















