Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
|
Articles:
VLAN Security - Making the Most of VLANs
| Read |
|
Articles:
VTP Pruning
| Read |
|
Articles:
VTP Protocol - In-Depth Analysis
| Read |
|
Articles:
VTP Introduction & Modes
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
VLANs - Access & Trunk Links
| Read |
|
Articles:
Dynamic VLANs
| Read |
|
Articles:
Static VLANs
| Read |
| Read | |
|
Articles:
The VLAN Concept - Introduction to VLANs
| Read |
Suggested Articles:

Network Fundamentals
Next-Gen Firewalls & Topologies. Designing & Bu...
Next-generation firewalls (NGFWs) and DMZ zones are two critical components of network security that work hand in hand to protect an organization's...
Subnetting
IP Subnet Calculator
This free online Subnet Calculator provides a fast and easy way to calculate all aspects of any IP Address and Subnet Mask. Simply enter your des...
Network Cabling
10Base-T/2/5/F/35 - Ethernet
The 10Base-T UTP Ethernet and 10Base-2 Coax Ethernet were very popular in the early to mid 1990's when 100 Mbps network cards and hubs/switches wer...

Network Fundamentals
DoS & DDoS Attacks
A Denial of Service (DoS) attack is a malicious attempt to disrupt the normal functioning of a website, server or network by flooding it with traff...
Featured Subcategories:
Netflow Articles:

Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...

Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...

Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...

NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...
Your IP address:
18.119.106.149
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
The VLAN Concept - Introduction to VLANs
We hear about them everywhere, vendors around the world are constantly trying to push them into every type of network and as a result, the Local Area Ne...

VLAN Networks
VTP Pruning
VTP (VLAN Trunking Protocol) pruning is a feature that is used in Cisco switches to reduce unnecessary traffic in VLAN (Virtual Local Area Network) trun...

VLAN Networks
VLAN InterSwitch Link (ISL) Protocol Analysis
Deciding whether to use ISL or IEEE 802.1q to power your trunk links can be quite confusing if you cannot identify the advantages and disadvantages of e...

VLAN Networks
Comparing Traditional Flat & VLAN Networks
Designing and building a network is not a simple job. VLANs are no exception to this rule, in fact they require a more sophisticated approach because of...
Routing
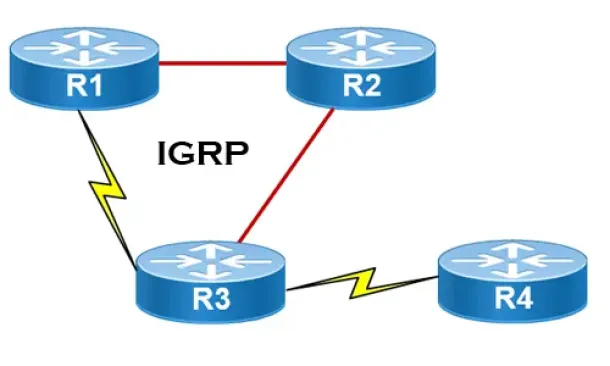
Interior Gateway Protocol - IGRP
IGRP (Interior Gateway Routing Protocol) is a Cisco proprietary distance-vector routing protocol used in enterprise networks to exchange routing informa...
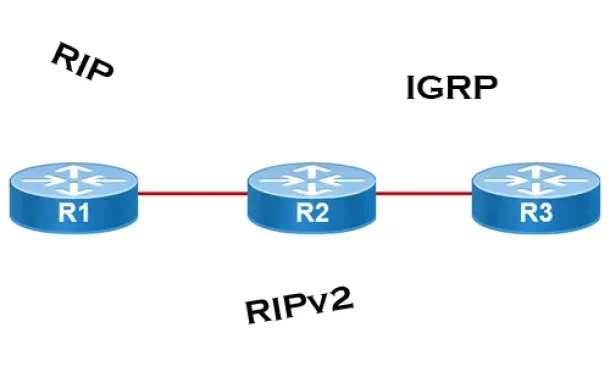
Routing
Distance Vector Routing Protocols
Distance Vector routing protocols use frequent broadcasts (255.255.255.255 or FF:FF:FF:FF) of their entire routing table every 30 sec. on all their inte...
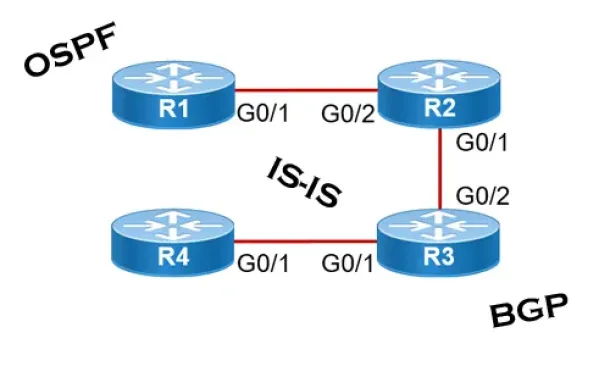
Routing
Link State Routing Protocols
Link State routing protocols do not view networks in terms of adjacent routers and hop counts, but they build a comprehensive view of the overall networ...
Routing
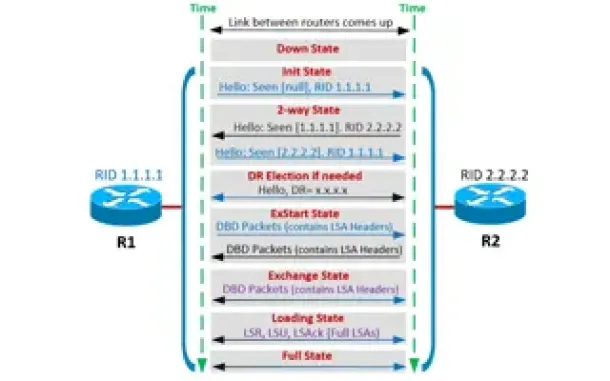
OSPF - Part 4: OSPF Neighbor States – OSPF Neighbor ...
This is the third article of our OSPF series which analyzes the different OSPF States routers go through during the OSPF discovery and neighbor forming ...
Virtualization & VM Backup
Understanding Deduplication. Complete Guide to Dedup...
When considering your VM backup solution, key features such as deduplication are incredibly important. This is not simply from a cost perspective but al...
Windows Servers
How to Enable ‘Web Server’ Certificate Template Opti...
In this article we will show you how to enable the ‘Web Server’ certificate template option on a Windows Certification Authority (Windows CA) Server.&nb...
Virtualization & VM Backup
SysAdmin Day 2020 - Get your Free Amazon Voucher & G...
SysAdmin Day has arrived, and with it, gratitude for all the unsung heroes that 2020 has needed. Your hard work has made it possible for all of us to ke...
Cisco Routers
Configuring PPTP (VPDN) Server On A Cisco Router
The Point to Point Tunneling Protocol (PPTP) is a network protocol used to create VPN tunnels between public networks. These VPN tunnels are encrypted f...




















