Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
|
Articles:
IP Subnet Calculator
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
Suggested Articles:
Network Cabling
Fibre Optic Cables - Single-Mode Multi-Mode - A...
In this article, we'll talk about Fiber optic cables and how it has changed the design and implementation of network infrastructures, providing hig...
The OSI Model
The OSI Model: Layer 5 - Session Layer
The Session layer is responsible for setting up, managing and then tearing down sessions between Presentation layer entities. The Session layer als...
Network Address Translation - NAT
The Network Address Translation Table
After that simple and informative introduction to the NAT concept, it's time to find out more about how it works and this is where the NAT table co...
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 3: TCP Header Len...
The third field under close examination is the TCP Header length. There really isn't that much to say about the Header length other than to explain...
Featured Subcategories:
Netflow Articles:

Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...

NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...

Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...

Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...
Your IP address:
3.138.33.55
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!

VLAN Networks
VLAN InterSwitch Link (ISL) Protocol Analysis
Deciding whether to use ISL or IEEE 802.1q to power your trunk links can be quite confusing if you cannot identify the advantages and disadvantages of e...

VLAN Networks
VLAN Security - Making the Most of VLANs
It's easy to see why virtual LANs have become extremely popular on networks of all sizes. In practical terms, multiple VLANs are pretty much the same as...
VLAN Networks
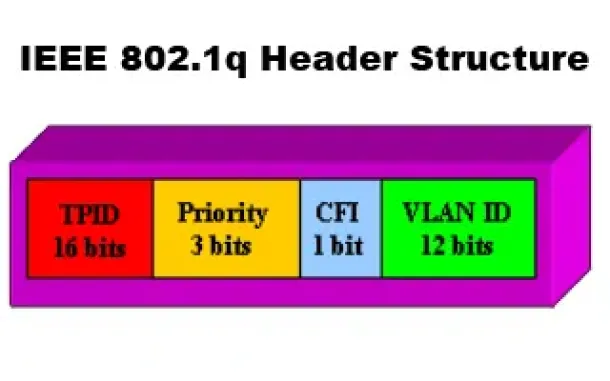
VLANs - IEEE 802.1q Trunk Link Protocol Analysis
While the VLAN Tagging article briefly covered the IEEE 802.1q protocol this article will continue building upon it by further analyzing the IEEE 802.1q...

VLAN Networks
VTP Introduction & Modes
The invention of VLANs was very much welcomed by all engineers and administrators, allowing them to extend, redesign and segment their existing network ...
Routing
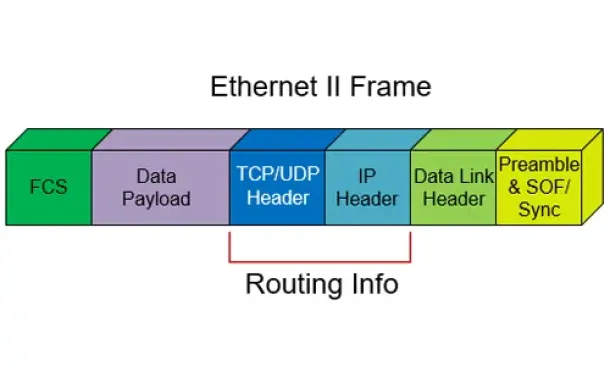
Routed Protocols
We all understand that TCP/IP, IPX-SPX are protocols which are used in a Local Area Network (LAN) so computers can communicate between with each other a...
Routing
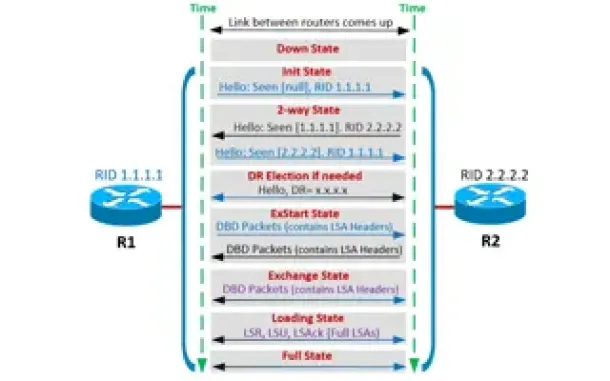
OSPF - Part 4: OSPF Neighbor States – OSPF Neighbor ...
This is the third article of our OSPF series which analyzes the different OSPF States routers go through during the OSPF discovery and neighbor forming ...
Routing
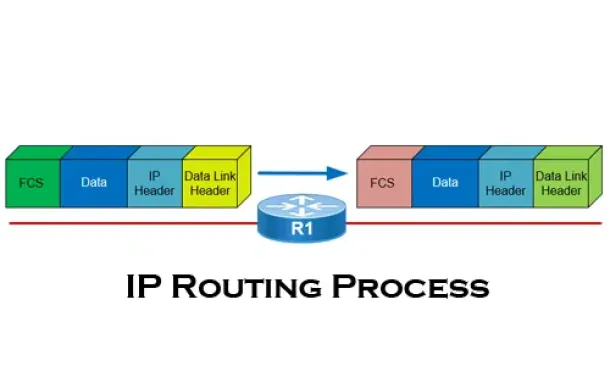
The IP Routing Process - Step-by-Step Analysis
We are going to analyse what happens when routing occurs on a network (IP routing process). When I was new to the networking area, I thought that all yo...
Routing
Hybrid Routing Protocols - Advantages and Disadvanta...
Hybrid routing protocols are a combination of distance-vector and link-state routing protocols, and are used to provide a more efficient and scala...
Cisco Firewalls
Understand & Configure NAT Reflection, NAT Loopback,...
This article examines the concept of NAT Reflection, also known as NAT Loopback or Hairpinning, and shows how to configure a Cisco ASA Firewall running ...
Windows Servers
Download Altaro Free VM Backup & Win a PlayStation 4...
We have some exciting news for you today!
Altaro has launched a great contest in celebration of SysAdmin Day on 27th July!
They will be giving away Am...
Cisco Routers
How To Configure Windows VPDN (PPTP) Dialup Connection
Setting up a Windows VPDN connection is a required task in order to connect to a remote network. In previous articles we covered the set up of a VPDN - ...
Cisco Routers
Cisco Router Password Recovery
Password recovery is a fairly frequently used procedure for administrators and engineers. Even though we usually stack our passwords in some word, excel...


















