Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
|
Articles:
802.3 Fast Ethernet (100 Mbit/Sec) Model
| Read |
|
Articles:
Migrating From Ethernet To Fast Ethernet
| Read |
| Read | |
| Read | |
|
Articles:
The Novell Proprietary Frame Format
| Read |
|
Articles:
The IEEE 802.3 SNAP Frame Format
| Read |
|
Articles:
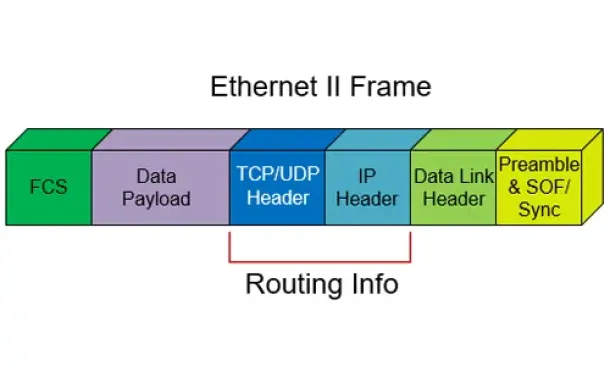
The Ethernet II Frame Format
| Read |
|
Articles:
The IEEE 802.3 Frame Format
| Read |
|
Articles:
Manchester Signal Encoding
| Read |
|
Articles:
IEEE 802.3 Interframe Spacing
| Read |
| Read | |
|
Articles:
Propagation Delay
| Read |
|
Articles:
Late Ethernet Collisions
| Read |
|
Articles:
Early Ethernet Collisions
| Read |
|
Articles:
Introduction to Ethernet Collisions
| Read |
|
Articles:
What is CSMA/CD ?
| Read |
Suggested Articles:
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 1: TCP Source & D...
This section contains one of the most well-known fields in the TCP header, the Source and Destination port numbers. These fields are used to specif...
Network Protocols
ISDN Layers, Protocols & Components
Our previous article was an Introduction To The ISDN Protocol. This article dives a bit deeper by examining ISDN Layers, Protocols & Components...
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 5: TCP Window Siz...
Our fifth section contains some very interesting fields that are used by the TCP transport protocol. We see how TCP helps control how much data is ...

Network Fundamentals
Measuring Network Performance: Test Network Thr...
Measuring network performance has always been a difficult and unclear task, mainly because most engineers and administrators are unsure which appro...
Featured Subcategories:
Netflow Articles:

Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...

Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...

Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...

NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...
Your IP address:
3.133.122.65
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
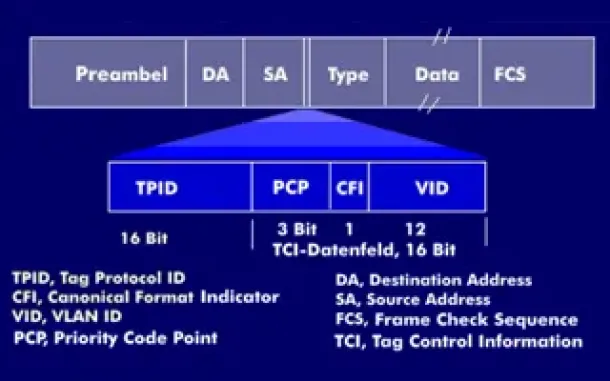
VLAN Tagging - Understanding VLANs Ethernet Frames
We mentioned that Trunk Links are designed to pass frames (packets) from all VLANs, allowing us to connect multiple switches together and independently ...

VLAN Networks
InterVLAN Routing - Routing between VLAN Networks
This article deals with the popular topic of InterVLAN routing, which is used to allow routing & communication between VLAN networks. Our article an...

VLAN Networks
VLANs - Access & Trunk Links
If you've read our previous article The VLAN Concept - Introduction to VLANs then you should feel comfortable with terms such as 'VLAN', 'Sta...
VLAN Networks
VTP Protocol - In-Depth Analysis
The previous article introduced the VTP protocol, we examined how it can be used within a network, to help manage VLANs and ease the administrative over...
Routing
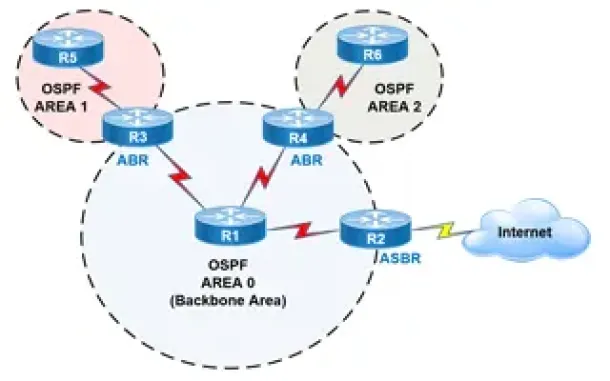
OSPF - Part 2: How OSPF Protocol Works & Basic Conce...
This article covers basic OSPF concepts and operation. We explain how OSPF works, how OSPF tables are built on an OSPF-enabled router and their purpose ...
Routing
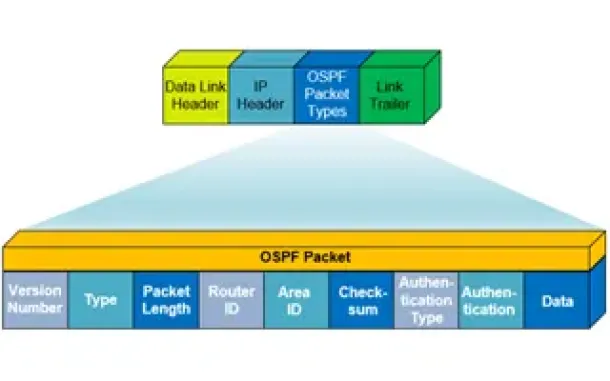
OSPF - Part 1: Introduction, OSPF Packet Structure, ...
Open Shortest Path First (OSPF) is a popular routing protocol developed for Internet Protocol (IP) networks by the Interior Gateway Protocol (IGP) worki...
Routing
Routed Protocols
We all understand that TCP/IP, IPX-SPX are protocols which are used in a Local Area Network (LAN) so computers can communicate between with each other a...
Routing
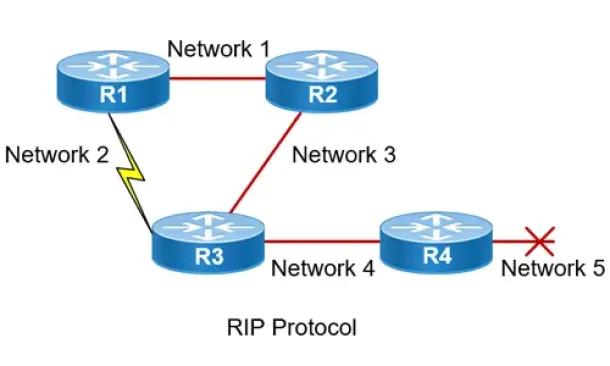
Routing Information Protocol - RIP
Routing Information Protocol (RIP) is a distance-vector routing protocol that is commonly used in small to medium-sized networks. It is one of the...
Cisco Wireless
Configuring Cisco WLC Link Aggregation (LAG) with Po...
Cisco Wireless Controllers (WLC) support the configuration of Link Aggregation (IEEE 802.3ad - LAG) which bundles the controller ports into a single por...
Windows Servers
Free Webinar & eBook on Microsoft Licensing for Virt...
Microsoft Licensing for Virtual environments can become a very complicated topic, especially with all the misconceptions and false information out there...
Windows Servers
Windows 2003 DNS Server Installation & Configuration
DNS is used for translating host names to IP addresses and the reverse, for both private and public networks (i.e.: the Internet). DNS does this by usin...
Palo Alto Networks
Complete Guide: Configuring IPSec VPN between Palo A...
This article will show you how to configure an IPSec VPN tunnel between a Palo Alto firewall (all PANOS versions) and Meraki MX security appliance. Our ...




















