Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
UDP Protocol - Header
| Read |
Suggested Articles:
Network Protocols
IPv6 - Analysing the IPv6 Protocol Structure an...
As discussed in the previous tutorial, we were made painfully aware that we were running out of IP address spaces and literally did in 2011. A ne...
Network Address Translation - NAT
Network Address Translation (NAT) Overload - Pa...
NAT Overload is the most common NAT method used throughout all networks that connect to the Internet. This is because of the way it functions and t...
The OSI Model
Data Encapsulation & Decapsulation in the OSI M...
Here we are going to explain in detail how data travels through the OSI model. You must keep in mind that the OSI model is a guideline. It tells th...
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 1: TCP Source & D...
This section contains one of the most well-known fields in the TCP header, the Source and Destination port numbers. These fields are used to specif...
Featured Subcategories:
Netflow Articles:

Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...

Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...

Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...

NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...
Your IP address:
3.144.13.33
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
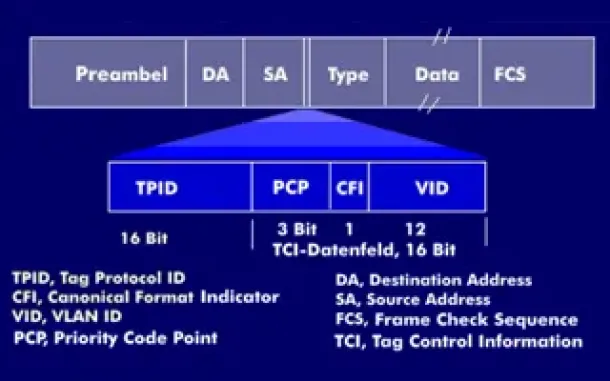
VLAN Tagging - Understanding VLANs Ethernet Frames
We mentioned that Trunk Links are designed to pass frames (packets) from all VLANs, allowing us to connect multiple switches together and independently ...

VLAN Networks
VLANs - Access & Trunk Links
If you've read our previous article The VLAN Concept - Introduction to VLANs then you should feel comfortable with terms such as 'VLAN', 'Sta...
VLAN Networks
Dynamic VLANs
Dynamic VLANs were introduced to grant the flexibility and complexity(!) that Static VLANs did not provide. Dynamic VLANs are quite rare because of thei...

VLAN Networks
VTP Introduction & Modes
The invention of VLANs was very much welcomed by all engineers and administrators, allowing them to extend, redesign and segment their existing network ...
Routing
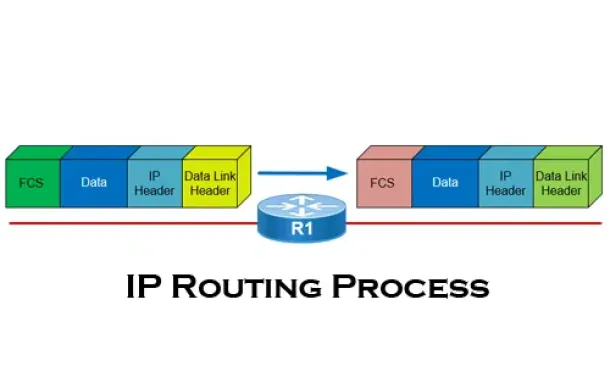
The IP Routing Process - Step-by-Step Analysis
We are going to analyse what happens when routing occurs on a network (IP routing process). When I was new to the networking area, I thought that all yo...
Routing
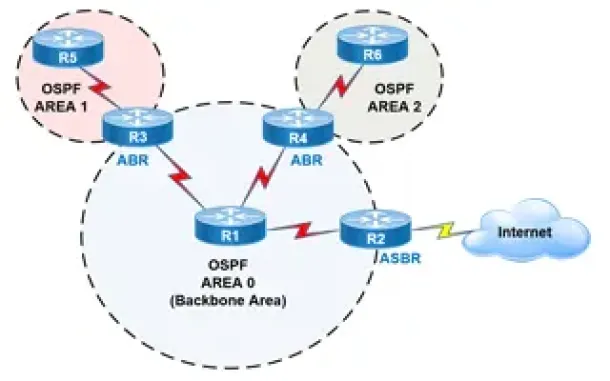
OSPF - Part 2: How OSPF Protocol Works & Basic Conce...
This article covers basic OSPF concepts and operation. We explain how OSPF works, how OSPF tables are built on an OSPF-enabled router and their purpose ...
Routing
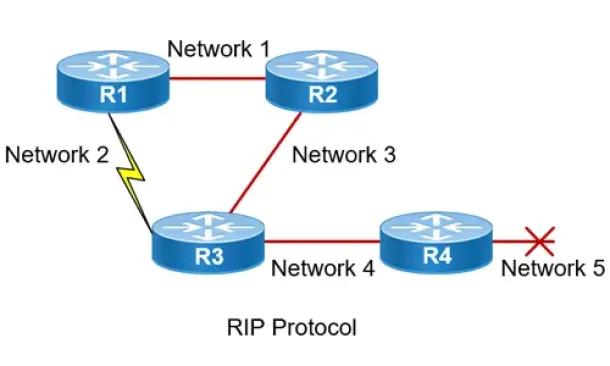
Routing Information Protocol - RIP
Routing Information Protocol (RIP) is a distance-vector routing protocol that is commonly used in small to medium-sized networks. It is one of the...
Routing
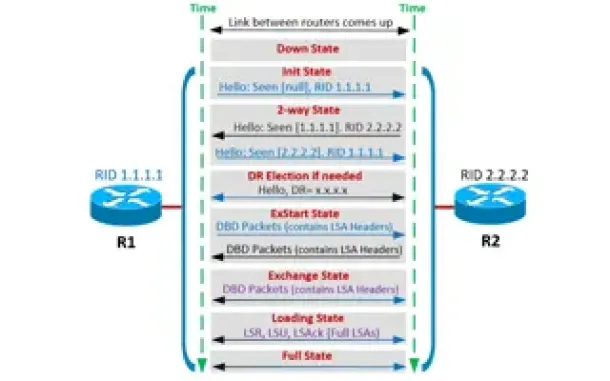
OSPF - Part 4: OSPF Neighbor States – OSPF Neighbor ...
This is the third article of our OSPF series which analyzes the different OSPF States routers go through during the OSPF discovery and neighbor forming ...
Windows Servers
The Importance of a Comprehensive Backup Strategy fo...
People and companies usually adopt a backup strategy suited to the needs of their working environment. As such, there is no absolute right or wrong meth...

Virtualization & VM Backup
Ultimate Guide: Install Windows 11 on VMware ESXi – ...
In this article, we’ll show you how to setup or install Microsoft Windows 11 on VMware’s ESXi servers and bypass the Trusted Platform Module version 2.0...
Cisco Wireless
Cisco Wireless Controllers (WLC) Datasheets Availabl...
We would like to inform our readers that Firewall.cx has just made available as a free download all of Cisco's Wireless Controller Datasheets.
The data...
Cisco Wireless
Understanding, Configuring & Tweaking Web-based Cisc...
Cisco Aironet Access Points, just like most Cisco devices, provide a web interface from which we are able to configure the device. It is often we are pr...


















