Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Linux File & Folder Permissions
| Read |
|
Articles:
Advanced Linux Commands
| Read |
|
Articles:
Installing Software On Linux
| Read |
|
Articles:
The Linux Command Line
| Read |
|
Articles:
The Linux File System
| Read |
|
Articles:
Why Use Linux?
| Read |
MS Server Articles:
Windows Servers
Free Hyper-V eBook - Create, Manage and Troublesh…
With the introduction of Hyper-V on the Windows Server platform, virtualization has quickly become the de facto standard for all companies seeking to…
Windows Servers
Understanding, Creating, Configuring & Applying W…
This article explains what Group Policies are and shows how to configure Windows Server 2012 Active Directory Group Policies. Our next article will c…
Windows Servers
Windows 2012 Server Foundation, Essential, Standa…
FREE Hyper-V & VMware Virtualization Backup: FREE for Firewall.cx readers for a Limited Time! Download Now!
Windows Server 2012 Edi…
Windows Servers
Creating a Virtual Machine in Windows Hyper-V. Co…
Our previous articles covered basic concepts of Virtualization along with the installation and monitoring of Windows 2012 Hyper-V. This article takes…
Featured Subcategories:
Virtualization & VM Backup Articles:
The Backup Bible. A Free Complete Guide to Disast…
The Free Backup Bible Complete Edition written by backup expert and Microsoft MVP Eric Siron, is comprised of 200+ pages of actionable content divide…

8 Critical Features to Have in a VM Backup Soluti…
Businesses that rely on virtual machines for their day-to-day operations should think twice about securing their infrastructure. Modern use of virtua…
FREE Webinar - Fast Track your IT Career with VMw…
Everyone who attends the webinar has a chance of winning a VMware VCP course (VMware Install, Config, Manage) worth $4,500!
Climbing the career ladd…
How to Fix VMware ESXi Virtual Machine 'Invalid S…
In this article, we'll show you how to deal with VMs which are reported to have an Invalid Status as shown in the screenshot below. This is a co…
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Linux - Unix
Configuring Linux to Act as a Firewall - Linux IPTable…
What exactly is a firewall? As in the non-computer world, a firewall acts as a physical barrier to prevent fires from spreading. In the computer world too…
Linux - Unix
Understanding The Linux Init Process & Different RunLe…
Different Linux systems can be used in many ways. This is the main idea behind operating different services at different operating levels. For example, th…
Linux - Unix
Linux BIND DNS - Part 4: Common BIND Files - Named.loc…
So far we have covered in great detail the main files required for the firewall.cx domain. These files, which we named db.firewall.cx and db.192.168.0, de…
Linux - Unix
The Linux Command Line
You could actually skip this whole section for those who are already familiar with the topic, but we highly recommend you read it because this is the hear…
Popular Topics
Cisco Routers
Cisco Router Basics
This article will focus on Cisco's routers which can be found in almost any organization due to their popularity and market penetration. Cisco has a numb…
Windows Workstations (XP, 7, 8, 10, 11)
How to Start Windows 8 and 8.1 in Safe Mode – Enabling…
This article will show you how to start Windows 8 and Windows 8.1 in Safe Mode and how to enable F8 Safe Mode. Previous Windows O/S users would recall tha…
Network Protocol Analyzers
How to Detect SYN Flood Attacks with Capsa Network Pro…
This article explains how to detect a SYN Flood Attack using an advanced protocol analyser like Colasoft Capsa. We’ll show you how to identify and inspect…
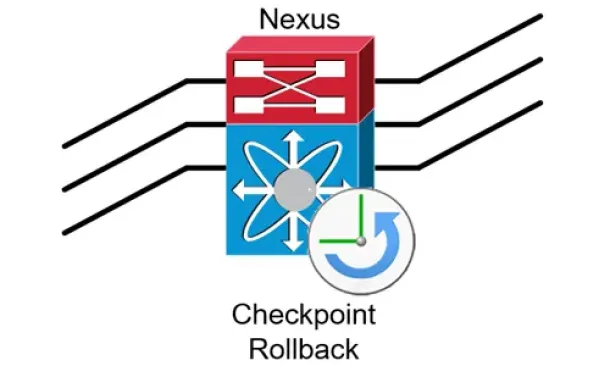
Cisco Data Center (Nexus/UCS)
Complete Guide to Nexus Checkpoint & Rollback Feature…
The Cisco NX-OS checkpoint feature provides the capability to capture at any time a snapshot (backup) of the Cisco Nexus configuration befo…


















