Suggested Articles:
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 3: TCP Header Lengt…
The third field under close examination is the TCP Header length. There really isn't that much to say about the Header length other than to explain w…
Subnetting
IP Subnetting - Part 4: Routing Between Subnets
Routing and Communication between subnets is the main topic here. This article analyses communications between subnets. We provide examples on differ…
Network Address Translation - NAT
Static NAT - Part 2
The previous page (Static NAT - Part 1) helped us understand what exactly happens with Static NAT and how it works, and we saw a few examples of how…
Network Cabling
Important Direct Cable Connection Notes
This page was designed to provide some notes on Direct Cable Connection (File-transfer) of Win9x/ME/2000 with LAPLINK (Printer port) Cable or Null-Mo…
Featured Subcategories:
Netflow Articles:

Complete Guide to Netflow: How Netflow & its Comp…
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive int…

Netflow: Monitor Bandwidth & Network Utilization…
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, applic…

NetFlow Analyzer: Free Download, Step-by-Step Ins…
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows w…

Netflow vs SNMP. Two Different Approaches to Netw…
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ne…
Your IP address:
66.249.73.68
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!

VLAN Networks
VTP Pruning
VTP (VLAN Trunking Protocol) pruning is a feature that is used in Cisco switches to reduce unnecessary traffic in VLAN (Virtual Local Area Network) trunks…

VLAN Networks
Comparing Traditional Flat & VLAN Networks
Designing and building a network is not a simple job. VLANs are no exception to this rule, in fact they require a more sophisticated approach because of t…

VLAN Networks
InterVLAN Routing - Routing between VLAN Networks
This article deals with the popular topic of InterVLAN routing, which is used to allow routing & communication between VLAN networks. Our article anal…

VLAN Networks
Static VLANs
VLANs are usually created by the network administrator, assigning each port of every switch to a VLAN. Depending on the network infrastructure and securit…
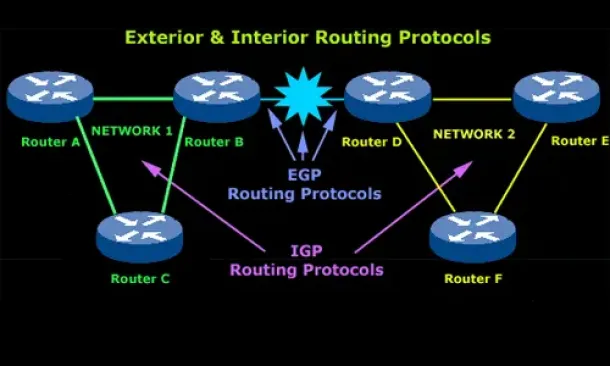
Routing
Introduction to Routing Protocols
Distance Vector, Link State RIP, IGRP, EIGRP, OSPF
Routing protocols were created for routers. These protocols have been designed to allow the exchange…
Routing
Routed Protocols
We all understand that TCP/IP, IPX-SPX are protocols which are used in a Local Area Network (LAN) so computers can communicate between with each other and…
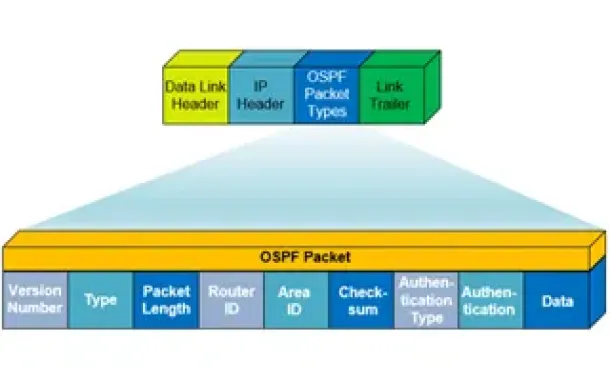
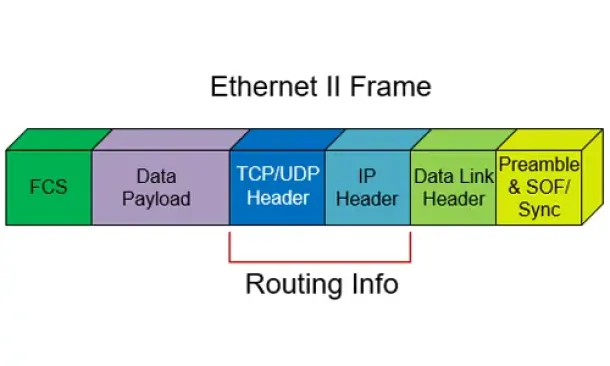
Routing
OSPF - Part 1: Introduction, OSPF Packet Structure, OS…
Open Shortest Path First (OSPF) is a popular routing protocol developed for Internet Protocol (IP) networks by the Interior Gateway Protocol (IGP) working…
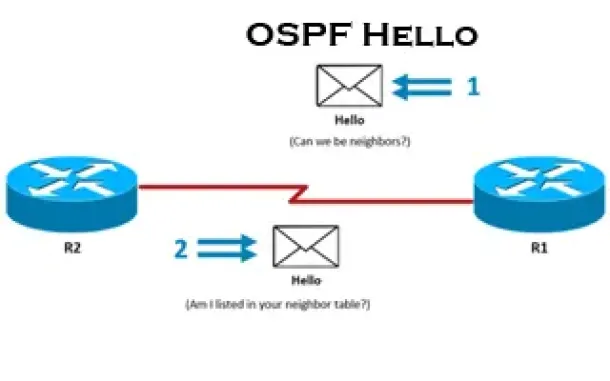
Routing
OSPF - Part 3: OSPF Adjacency & Neighbor Forming Proce…
This is the thrid article of our 6-part OSPF series (see below) that describes how OSPF routers perform neighbor relationship and adjacency. We’ll examine…
SASE & SD-WAN Networks
The Need for a Converged SASE Platform. Converging Net…
The digital transformation is pushing applications to the cloud, the 2020-2022 pandemic shifted employees to work from home, and the number of resulting n…
Cisco Firewalls
Upgrading - Uploading AnyConnect Secure Mobility Clien…
This article will show how to download and upload the newer AnyConnect 4.x VPN clients to your Cisco ASA Firewall appliance (5500 & 5500-X Series) and…
Cisco Routers
Cisco GRE and IPSec - GRE over IPSec - Selecting and C…
GRE Tunnels are very common amongst VPN implementations thanks to their simplicity and ease of configuration. With broadcasting and multicasting support…
Network Protocol Analyzers
How to Reconstruct HTTP Packets/Data & Monitor HTTP Us…
HTTP reconstruction is an advanced network security feature offered by nChronos version 4.3.0 and later. nChronos is a Network Forensic Analysis applicati…


















