Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
ICMP Protocol - Part 1: Introduction
| Read |
Suggested Articles:
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 1: TCP Source & D...
This section contains one of the most well-known fields in the TCP header, the Source and Destination port numbers. These fields are used to specif...
Ethernet Protocol, CSMA/CD, Collisions
The Ethernet II Frame Format
The following is a description of the frame format described by the original Ethernet Version II specification as released by DEC, Intel, and Xerox...
TCP - UDP Protocol Analysis
Transmission Control Protocol - Part 4: In-Dept...
This article is an introduction to the 7-page TCP Header analysis section that follows. We briefly view each section of the TCP Header and then mov...
Ethernet Protocol, CSMA/CD, Collisions
Early Ethernet Collisions
In this example, we will refer to an imaginary Ethernet network consisting of Stations A and B and any number of other stations. The status of the ...
Featured Subcategories:
Netflow Articles:

Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...

Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...

NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...

Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...
Your IP address:
18.223.106.232
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!

VLAN Networks
VTP Pruning
VTP (VLAN Trunking Protocol) pruning is a feature that is used in Cisco switches to reduce unnecessary traffic in VLAN (Virtual Local Area Network) trun...

VLAN Networks
VLAN InterSwitch Link (ISL) Protocol Analysis
Deciding whether to use ISL or IEEE 802.1q to power your trunk links can be quite confusing if you cannot identify the advantages and disadvantages of e...

VLAN Networks
VLAN Security - Making the Most of VLANs
It's easy to see why virtual LANs have become extremely popular on networks of all sizes. In practical terms, multiple VLANs are pretty much the same as...

VLAN Networks
Static VLANs
VLANs are usually created by the network administrator, assigning each port of every switch to a VLAN. Depending on the network infrastructure and secur...
Routing
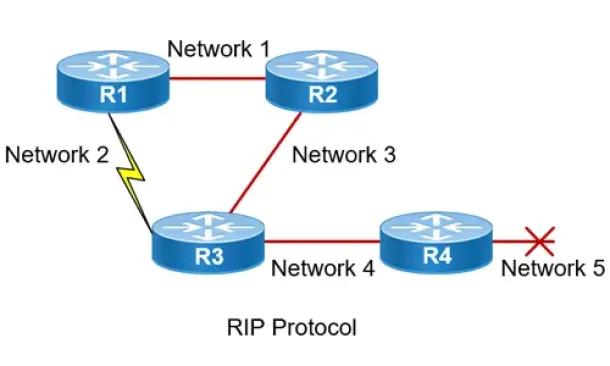
Routing Information Protocol - RIP
Routing Information Protocol (RIP) is a distance-vector routing protocol that is commonly used in small to medium-sized networks. It is one of the...
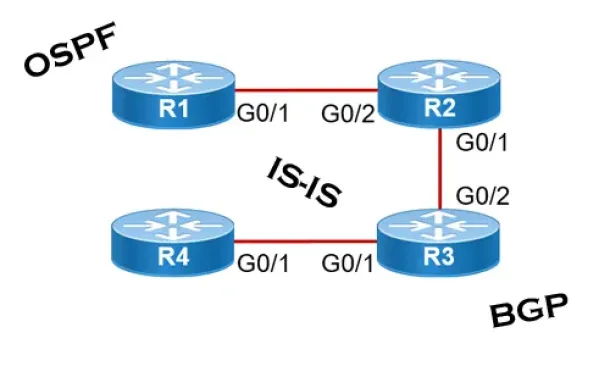
Routing
Link State Routing Protocols
Link State routing protocols do not view networks in terms of adjacent routers and hop counts, but they build a comprehensive view of the overall networ...
Routing
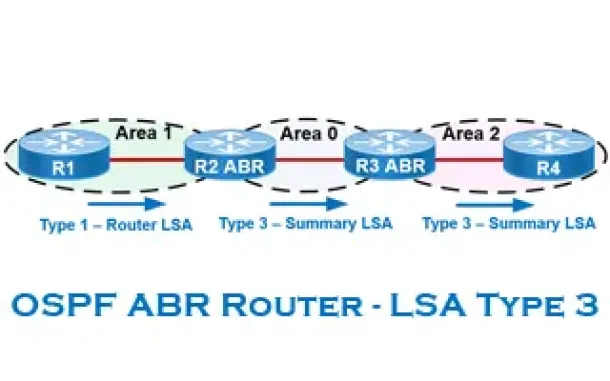
OSPF - Part 6: OSPF LSA Types - Purpose and Function...
Our previous article explained the purpose of Link State Update (LSU) packets and examined the Link State Advertisement (LSA) information contained with...
Routing
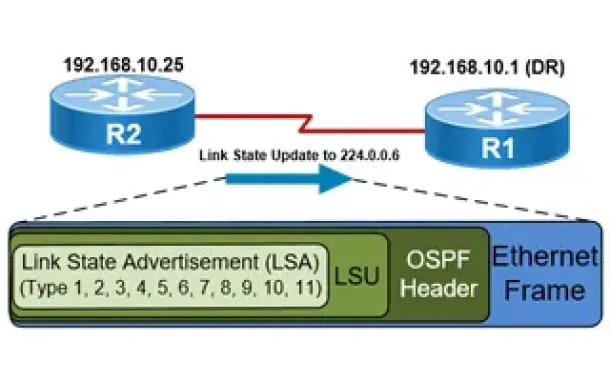
OSPF - Part 5: Analysis of OSPF Link State Update (L...
This article explains how OSPF uses Link State Advertisement (LSA) to exchange information about the network topology between routers. When a router rec...
Cisco Routers
Disabling Cisco Router Password Recovery Service
Most Cisco engineers are aware of the classic Password-Recovery service Cisco equipment have. If the device's credentials are lost, then performing the ...
Virtualization & VM Backup
6 Key Areas to Consider When Selecting a VM Backup S...
Backup and Disaster recovery are core considerations for any business with an IT footprint, whether that is on-premises or in the cloud.
Your business ...
Windows Servers
New Features in Windows Server 2012 - Why Upgrade t...
There is no doubt that Cloud Computing is hot topic these days. Innovations in cloud computing models have made every industry and company IT department...
Cisco Routers
Cisco Router Basics
This article will focus on Cisco's routers which can be found in almost any organization due to their popularity and market penetration. Cisco has a nu...


















