Network Fundamentals: Top Picks
Network Fundamentals
LAN Network Topologies
Network topologies can take a bit of time to understand when you're all new to this kind of cool stuff, but it's very important to fully understand t…
Network Fundamentals
The Importance of a Network Analyzer – Packet Sni…
Network Analyzers, also known as Packet Sniffers, are amongst the most popular network tools found inside any Network Engineer’s toolkit. A Network A…
Network Fundamentals
Network Data Transmission
Network data transmission refers to the process of sending and receiving information between two or more devices connected to a network. It is a crit…
Network Fundamentals
Network Broadcast
The term "Broadcast" is used very frequently in the networking world . You will see it in most networking books and articles, or see it happening on…
Featured Subcategories:
Netflow Articles:
Netflow
Complete Guide to Netflow: How Netflow & its Comp…
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive int…
Netflow
Netflow: Monitor Bandwidth & Network Utilization…
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, applic…
Netflow
Netflow vs SNMP. Two Different Approaches to Netw…
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ne…
Netflow
NetFlow Analyzer: Free Download, Step-by-Step Ins…
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows w…
Network Protocols:
TCP - UDP Protocol Analysis
Transmission Control Protocol - Part 4: In-Depth…
This article is an introduction to the 7-page TCP Header analysis section that follows. We briefly view each section of the TCP Header and then move…
Domain Name System (DNS)
The DNS Protocol - Part 2: DNS Queries & Resoluti…
This section will help you understand how the DNS queries work on the Internet and your home network. There are two ways to use the domain name syste…
Supernetting & CIDR
What is Supernetting (Route Summarization) & How…
Supernetting is the opposite of of subnetting, and is also known as route aggregation or CIDR (Classless Inter-Domain Routing). Supernetting is a tec…
IP Protocol
IP Protocol - Part 2: The Internet Protocol (IP)…
This article examines the Internet Protocol (IP) and its position within the OSI Model. We take a look at the IP Header and all fields contained with…
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 4: TCP Flag Options
As we have seen in the previous pages, some TCP segments carry data while others are simple acknowledgements for previously received data. The popula…
Subnetting
IP Subnetting - Part 3: Subnet Mask Bits & Analys…
So we have covered to some depth the subnetting topic, but there is still much to learn ! We are going to explain here the available subnet masks and…
Subnetting
IP Subnet Calculator
This free online Subnet Calculator provides a fast and easy way to calculate all aspects of any IP Address and Subnet Mask. Simply enter your desir…
Supernetting & CIDR
The Supernetting / CIDR Chart
This articles build upon our previous pages covering what is Supernetting (Route Summarization) & How Supernets Work and Supernetting In-De…
STP/ICMP Protocols:
ICMP Protocol
ICMP Protocol - Part 7: Time Exceeded Message Ana…
The ICMP - Time Exceeded message is one which is usually created by gateways or routers. In order to fully understand this ICMP message, you must be…
ICMP Protocol
ICMP Protocol - Part 5: Source Quench Message Ana…
The ICMP - Source Quench message is one that can be generated by either a gateway or host. You won't see any such message pop up on your workstation…
ICMP Protocol
ICMP Protocol - Part 6: Redirect Messages
The ICMP - Redirect Message is always sent from a gateway to the host and the example below will illustrate when this is used.
Putting it simply (be…

Spanning Tree Protocol (STP)
Spanning Tree Protocol – Part 1: Understand STP P…
One of the most used terms in network is LAN (Local Area Network). It’s a form of network that we encounter in our daily lives, at home, at work, stu…
Your IP address:
3.143.111.52
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
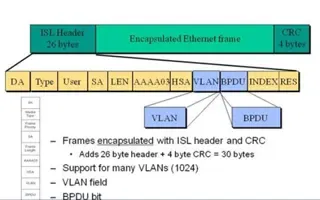
VLAN Networks
VLAN InterSwitch Link (ISL) Protocol Analysis
Deciding whether to use ISL or IEEE 802.1q to power your trunk links can be quite confusing if you cannot identify the advantages and disadvantages of eac…

VLAN Networks
Static VLANs
VLANs are usually created by the network administrator, assigning each port of every switch to a VLAN. Depending on the network infrastructure and securit…

VLAN Networks
VTP Pruning
VTP (VLAN Trunking Protocol) pruning is a feature that is used in Cisco switches to reduce unnecessary traffic in VLAN (Virtual Local Area Network) trunks…

VLAN Networks
VLANs - Access & Trunk Links
If you've read our previous article The VLAN Concept - Introduction to VLANs then you should feel comfortable with terms such as 'VLAN', 'Stati…
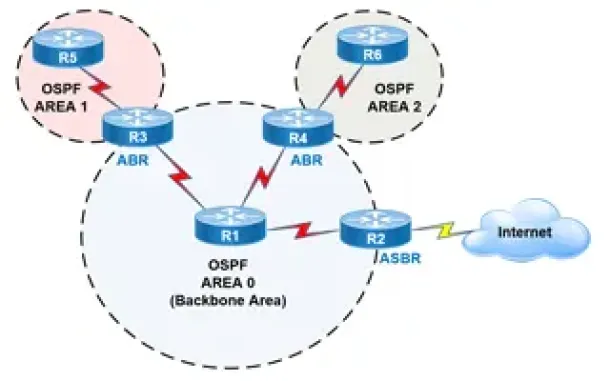
Routing
OSPF - Part 2: How OSPF Protocol Works & Basic Concept…
This article covers basic OSPF concepts and operation. We explain how OSPF works, how OSPF tables are built on an OSPF-enabled router and their purpose (N…
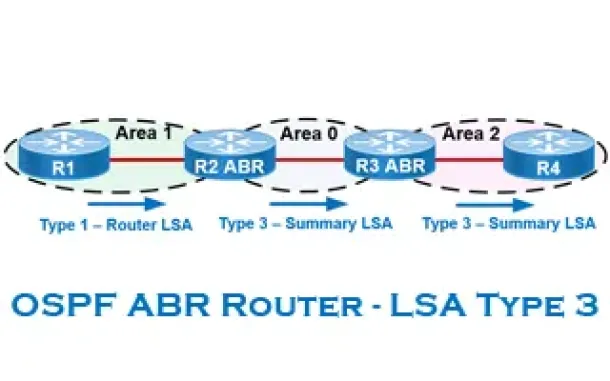
Routing
OSPF - Part 6: OSPF LSA Types - Purpose and Function o…
Our previous article explained the purpose of Link State Update (LSU) packets and examined the Link State Advertisement (LSA) information contained within…
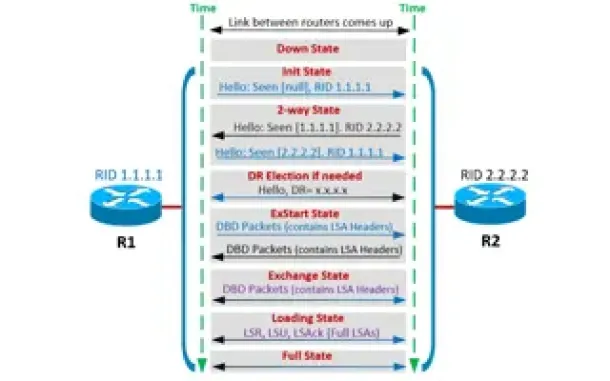
Routing
OSPF - Part 4: OSPF Neighbor States – OSPF Neighbor Fo…
This is the third article of our OSPF series which analyzes the different OSPF States routers go through during the OSPF discovery and neighbor forming pr…
Routing
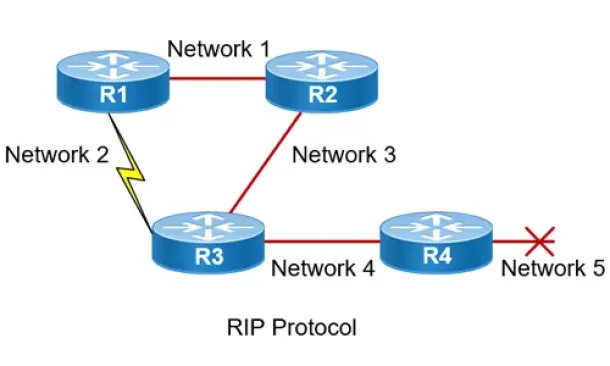
Routing Information Protocol - RIP
Routing Information Protocol (RIP) is a distance-vector routing protocol that is commonly used in small to medium-sized networks. It is one of the o…
Network Address Translation - NAT
Static NAT - Part 2
The previous page (Static NAT - Part 1) helped us understand what exactly happens with Static NAT and how it works, and we saw a few examples of how to us…
Network Address Translation - NAT
Network Address Translation (NAT) Overload - Part 1
NAT Overload is the most common NAT method used throughout all networks that connect to the Internet. This is because of the way it functions and the limi…
Network Address Translation - NAT
Dynamic NAT - Part 2
Our previous article, Dynamic NAT - Part 1, covered the basic idea of Dynamic Network Address Translation. We are now going to take a closer look at the p…
Network Address Translation - NAT
Network Address Translation (NAT) Overload - Part 2
In our previous article, Network Address Translation (NAT) Overload - Part 1, we explained what NAT Overload is and how it works. This page deals with the…


















