Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
|
Articles:
Direct Cable Connection
| Read |
| Read | |
| Read | |
| Read | |
|
Articles:
Important Direct Cable Connection Notes
| Read |
| Read | |
|
Articles:
100Base-(T) TX/T4/FX - Ethernet
| Read |
|
Articles:
10Base-T/2/5/F/35 - Ethernet
| Read |
| Read | |
|
Articles:
Straight Thru UTP Cables
| Read |
| Read | |
Suggested Articles:
Network Address Translation - NAT
Network Address Translation (NAT) Overload - Pa...
In our previous article, Network Address Translation (NAT) Overload - Part 1, we explained what NAT Overload is and how it works. This page deals w...
The OSI Model
The OSI Model: Layer 5 - Session Layer
The Session layer is responsible for setting up, managing and then tearing down sessions between Presentation layer entities. The Session layer als...
Ethernet Protocol, CSMA/CD, Collisions
Ethernet Troubleshooting - Physical Frame Corru...
When troubleshooting your Ethernet network, the first thing to look for is physical frame corruption. In this essay, we will discuss the different ...
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 7: TCP Data Paylo...
Finally, the last page of our incredible TCP Analysis. As most of you would expect, this section is dedicated to the DATA section that follows the ...
Featured Subcategories:
Netflow Articles:

Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...

Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...

Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...

NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...
Your IP address:
18.221.21.111
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!

VLAN Networks
Static VLANs
VLANs are usually created by the network administrator, assigning each port of every switch to a VLAN. Depending on the network infrastructure and secur...

VLAN Networks
VLANs - Access & Trunk Links
If you've read our previous article The VLAN Concept - Introduction to VLANs then you should feel comfortable with terms such as 'VLAN', 'Sta...
VLAN Networks
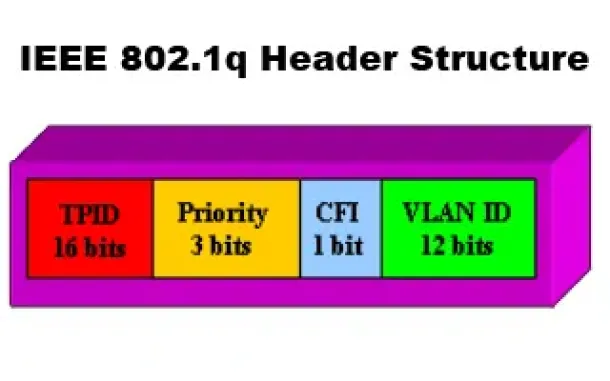
VLANs - IEEE 802.1q Trunk Link Protocol Analysis
While the VLAN Tagging article briefly covered the IEEE 802.1q protocol this article will continue building upon it by further analyzing the IEEE 802.1q...

VLAN Networks
Comparing Traditional Flat & VLAN Networks
Designing and building a network is not a simple job. VLANs are no exception to this rule, in fact they require a more sophisticated approach because of...
Routing
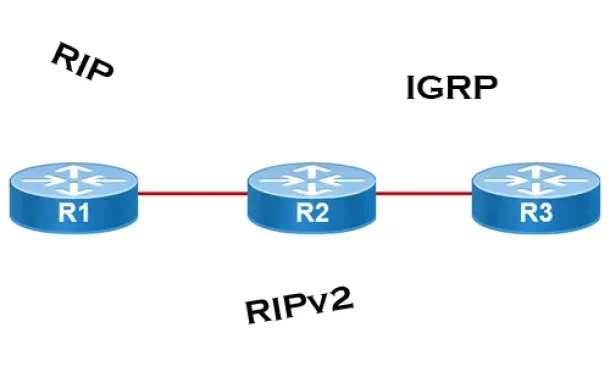
Distance Vector Routing Protocols
Distance Vector routing protocols use frequent broadcasts (255.255.255.255 or FF:FF:FF:FF) of their entire routing table every 30 sec. on all their inte...
Routing
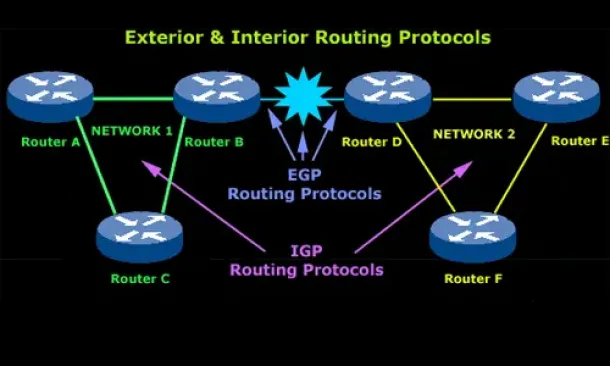
Introduction to Routing Protocols
Distance Vector, Link State RIP, IGRP, EIGRP, OSPF
Routing protocols were created for routers. These protocols have been designed to allow the exchan...
Routing
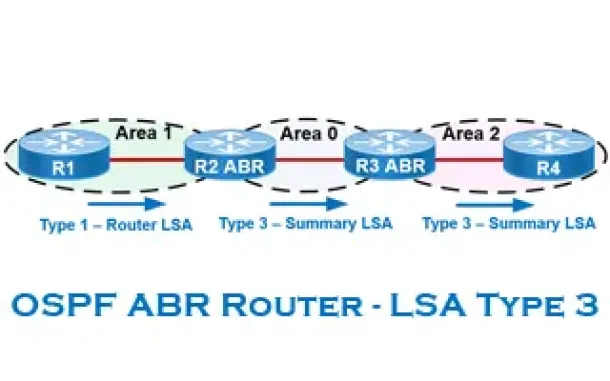
OSPF - Part 6: OSPF LSA Types - Purpose and Function...
Our previous article explained the purpose of Link State Update (LSU) packets and examined the Link State Advertisement (LSA) information contained with...
Routing
Hybrid Routing Protocols - Advantages and Disadvanta...
Hybrid routing protocols are a combination of distance-vector and link-state routing protocols, and are used to provide a more efficient and scala...
Cisco Wireless
Cisco WLC Interfaces, Ports & Their Functionality. U...
Our previous article introduced Cisco’s popular Wireless ControllerCisco’s popular Wireless Controller (WLC) devices and examined their benefits to ente...
Windows Servers
Windows 2012 Server NIC Teaming – Load Balancing/Fai...
NIC Teaming, also known as Windows Load Balancing or Failover (LBFO), is an extremely useful feature supported by Windows Server 2012 that allows the ag...
Windows Servers
Guide to Windows Server 2016 Hyper-V Hypervisor: New...
One of Windows Server 2016 highlights is the newer Hyper-V server that not only extends the hypervisor’s features and capabilities but also introduces a...
Cisco Routers
Troubleshooting PPP Internet Connection On A Cisco R...
The Point-to-Point Protocol is one of the most popular protocols around used by engineers, ISPs and companies around the globe for authentication of rem...


















