Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Renaming Windows 2000 Domain Name
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
MS Server Articles:
Windows Servers
Easy, Fast & Reliable Hyper-V & VMware Backup w...
As more companies around the world adopt the virtualization technology to increase efficiency and productivity, Microsoft’s Hyper-V virtualization ...
Windows Servers
How to Install Windows 2012 Hyper-V via Server ...
Our previous article covered the basic concepts of Virtualization and Windows Server 2012 Hyper-V. This article takes a closer look at Micros...
Windows Servers
How to Install and Configure Windows 2012 DNS S...
Our previous article covered introduction to the Domain Name System (DNS) and explained the importance of the DNS Server role within the network in...
Windows Servers
Windows Server 2016 VM Backup with Altaro's New...
Altaro has released Altaro VM Backup, a faster and lighter upgrade to its flagship Hyper-V and VMware backup solution, which now supports all Windo...
Featured Subcategories:
Virtualization & VM Backup Articles:
5 Most Critical Microsoft M365 Vulnerabilities ...
Microsoft 365 is an incredibly powerful software suite for businesses, but it is becoming increasingly targeted by people trying to steal your data...
Understanding Deduplication. Complete Guide to ...
When considering your VM backup solution, key features such as deduplication are incredibly important. This is not simply from a cost perspective b...

8 Critical Features to Have in a VM Backup Solu...
Businesses that rely on virtual machines for their day-to-day operations should think twice about securing their infrastructure. Modern use of virt...
Differences Between VMware vSphere, vCenter, ES...
In this article we will cover the differences between VMware ESXi, vSphere and vCenter while also explain the features supported by each vSphere ed...
Your IP address:
3.142.172.36
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Linux - Unix
Installation and Configuration of Linux DHCP Server
For a cable modem or a DSL connection, the service provider dynamically assigns the IP address to your PC. When you install a DSL or a home cable router...
Linux - Unix
Configuring Linux to Act as a Firewall - Linux IPTab...
What exactly is a firewall? As in the non-computer world, a firewall acts as a physical barrier to prevent fires from spreading. In the computer world t...
Linux - Unix
Linux System Resource & Performance Monitoring
You may be a user at home, a user in a LAN (local area network), or a system administrator of a large network of computers. Alternatively, you may be ma...
Linux - Unix
Working with Linux TCP/IP Network Configuration Files
This article covers the main TCP/IP network configuration files used by Linux to configure various network services of the system such as IP Address, De...
Popular Topics
Cisco Routers
Configuring NAT Overload On A Cisco Router
NAT (Network Address Translation) is a method that allows the translation (modification) of IP addresses while packets/datagrams are traversing the netw...
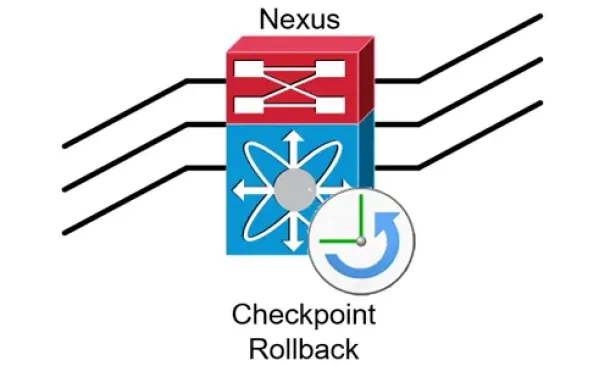
Cisco Data Center (Nexus/UCS)
Complete Guide to Nexus Checkpoint & Rollback Featur...
The Cisco NX-OS checkpoint feature provides the capability to capture at any time a snapshot (backup) of the Cisco Nexus configuration be...
Cisco Routers
Cisco Type 7 Password Decrypt / Decoder / Crack Tool
The Firewall.cx Cisco Password Decoder Tool (see below) provides readers with the ability to decrypt 'Type 7' cisco passwords.
For security reasons, we...

OpManager - Network Monitoring & Management
Elevate your network management: Maximizing efficien...
As technology evolves, so do our networks. Today's sprawling network infrastructures are intricate ecosystems, demanding more from IT teams than ever be...

















