Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
|
Articles:
Firewall.cx Free Cisco Lab: Our Partners
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
Suggested Articles:
Network Protocol Analyzers
Introducing Colasoft Unified Performance Manage...
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, qua...
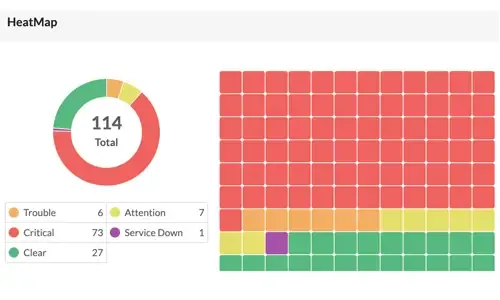
OpManager - Network Monitoring & Management
Boost Network Security and Efficiency with Inte...
Network alerts are vital for maintaining your network's health, efficiency, and security, ensuring seamless daily operations. They act as an early ...
Network Protocol Analyzers
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...
Network Protocol Analyzers
How to Perform TCP SYN Flood DoS Attack & Detec...
This article will help you understand TCP SYN Flood Attacks, show how to perform a SYN Flood Attack (DoS attack) using Kali Linux & hping3 and ...
Featured Subcategories:
WireShark Articles:
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing proce...
Advanced Network Protocol Analyzer Review: Cola...
Firewall.cx has covered Colasoft Capsa several times in the past, but its constant improvements make it well worth revisiting. Since the last revie...
How To Detect ARP Attacks & ARP Flooding With C...
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC addr...
How to Detect SYN Flood Attacks with Capsa Netw...
This article explains how to detect a SYN Flood Attack using an advanced protocol analyser like Colasoft Capsa. We’ll show you how to identify and ...
Your IP address:
18.224.32.18
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!

Palo Alto Networks
How to Manually Download, Import & Install PAN-OS on...
This article provides comprehensive guidance on the manual processes involved in downloading, uploading, and installing (import) any PAN-OS version on a...
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial Conf...
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Firew...
Palo Alto Networks
How to Register a Palo Alto Firewall and Activate Su...
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product upda...
Palo Alto Networks
Complete Guide: Configuring IPSec VPN between Palo A...
This article will show you how to configure an IPSec VPN tunnel between a Palo Alto firewall (all PANOS versions) and Meraki MX security appliance. Our ...
Windows Servers
How to Install Windows 2012 Hyper-V via Server Manag...
Our previous article covered the basic concepts of Virtualization and Windows Server 2012 Hyper-V. This article takes a closer look at Microsoft’s...
Windows Servers
Windows 2003 DHCP Server Advanced Configuration - Pa...
Part 1 of our Windows 2003 DHCP Server Advanced Configuration article explained the creation and configuration of DHCP Scope options and how to configur...
Windows Servers
New Features in Windows Server 2012 - Why Upgrade t...
There is no doubt that Cloud Computing is hot topic these days. Innovations in cloud computing models have made every industry and company IT department...
Windows Servers
Guide to Windows Server 2016 Hyper-V Hypervisor: New...
One of Windows Server 2016 highlights is the newer Hyper-V server that not only extends the hypervisor’s features and capabilities but also introduces a...
Popular Topics
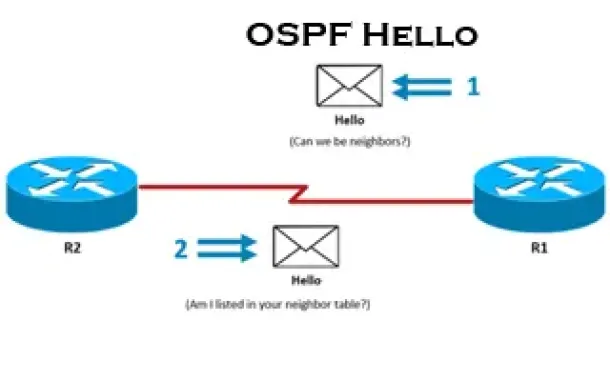
Routing
OSPF - Part 3: OSPF Adjacency & Neighbor Forming Pro...
This is the thrid article of our 6-part OSPF series (see below) that describes how OSPF routers perform neighbor relationship and adjacency. We’ll exami...
VLAN Networks
The VLAN Concept - Introduction to VLANs
We hear about them everywhere, vendors around the world are constantly trying to push them into every type of network and as a result, the Local Area Ne...
SASE & SD-WAN Networks
SD-WAN is the Emerging, Evolving Solution for the Br...
A lot has changed in how people work during the past twenty years. Co-working spaces, mobility, and the cloud now are common. Businesses are spread out ...
Windows Servers
Configuring Domain Group Policy for Windows 2003
Windows 2003 Group Policies allow the administrators to manage a group of people accessing a resource efficiently. The group policies can be used to con...
Cisco Switches
Basic & Advanced Catalyst Layer 3 Switch Configurati...
This article covers basic and advanced configuration of Cisco Catalyst Layer-3 switches such as the Cisco Catalyst 3560G, 3560E, 3560-X, 3750, 3750E, 37...
Cisco Services & Technologies
Fix Cisco VPN Client Break After Windows 10 Annivers...
Windows 10 latest update 1607 code named Anniversary update promises to introduce a number of significant enhancements including breaking your trustwort...
Cisco CallManager-CCME
Cisco CallManager Express Basic Concepts - Part 2
Our previous article, Cisco CallManager Express Basic Concepts - Part 1 covered the very basic concepts of CCME and its operation. This article continue...
Cisco CallManager-CCME
CallManager Express GUI Software Installation & Conf...
Cisco CallManager Express, also known as CME or CCME, runs on both Cisco ISR Routers and UC500 platform, including UC520, UC540 and UC560.
CallManager ...


















