Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
|
Articles:
802.3 Fast Ethernet (100 Mbit/Sec) Model
| Read |
|
Articles:
Migrating From Ethernet To Fast Ethernet
| Read |
| Read | |
| Read | |
|
Articles:
The Novell Proprietary Frame Format
| Read |
|
Articles:
The IEEE 802.3 SNAP Frame Format
| Read |
|
Articles:
The Ethernet II Frame Format
| Read |
|
Articles:
The IEEE 802.3 Frame Format
| Read |
|
Articles:
Manchester Signal Encoding
| Read |
|
Articles:
IEEE 802.3 Interframe Spacing
| Read |
| Read | |
|
Articles:
Propagation Delay
| Read |
|
Articles:
Late Ethernet Collisions
| Read |
|
Articles:
Early Ethernet Collisions
| Read |
|
Articles:
Introduction to Ethernet Collisions
| Read |
|
Articles:
What is CSMA/CD ?
| Read |
Suggested Articles:
TCP - UDP Protocol Analysis
Transmission Control Protocol - Part 4: In-Depth…
This article is an introduction to the 7-page TCP Header analysis section that follows. We briefly view each section of the TCP Header and then move…
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 4: TCP Flag Options
As we have seen in the previous pages, some TCP segments carry data while others are simple acknowledgements for previously received data. The popula…
ICMP Protocol
ICMP Protocol - Part 2: Echo / Echo Reply (Ping)…
As mentioned in the previous page, an Echo is simply what we networking engineers call a 'ping'. The Echo Reply is, as most would guess, the 'p…
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 3: TCP Header Lengt…
The third field under close examination is the TCP Header length. There really isn't that much to say about the Header length other than to explain w…
Featured Subcategories:
Netflow Articles:

Bandwidth Detective: Uncover Hidden Traffic and E…
In this article, we explore the core principles of bandwidth management and examine how modern network monitoring technologies can assist in maintain…

Netflow vs SNMP. Two Different Approaches to Netw…
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ne…

NetFlow Analyzer: Free Download, Step-by-Step Ins…
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows w…

Netflow: Monitor Bandwidth & Network Utilization…
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, applic…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
VTP Protocol - In-Depth Analysis
The previous article introduced the VTP protocol, we examined how it can be used within a network, to help manage VLANs and ease the administrative overhe…

VLAN Networks
Comparing Traditional Flat & VLAN Networks
Designing and building a network is not a simple job. VLANs are no exception to this rule, in fact they require a more sophisticated approach because of t…

VLAN Networks
VTP Introduction & Modes
The invention of VLANs was very much welcomed by all engineers and administrators, allowing them to extend, redesign and segment their existing network wi…
VLAN Networks
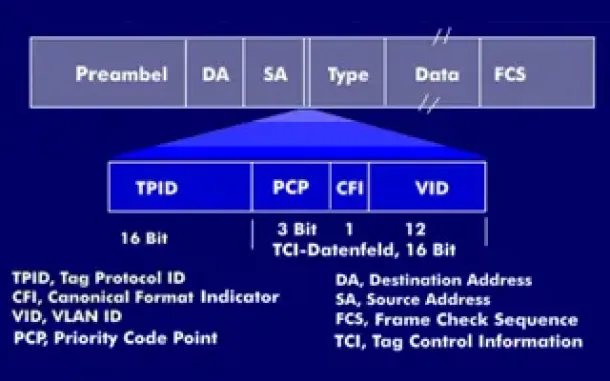
VLAN Tagging - Understanding VLANs Ethernet Frames
We mentioned that Trunk Links are designed to pass frames (packets) from all VLANs, allowing us to connect multiple switches together and independently co…
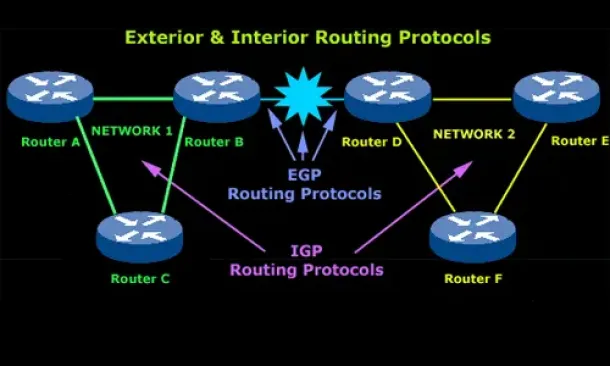
Routing
Introduction to Routing Protocols
Distance Vector, Link State RIP, IGRP, EIGRP, OSPF
Routing protocols were created for routers. These protocols have been designed to allow the exchange…
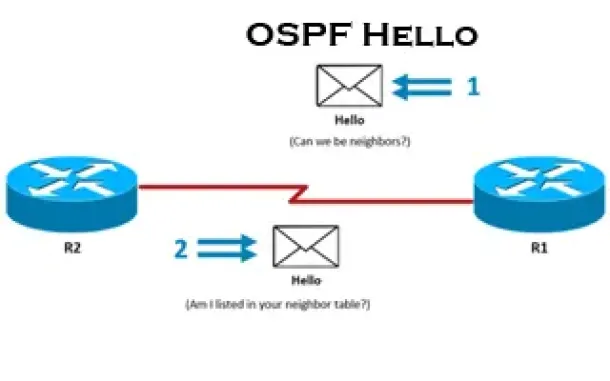
Routing
OSPF - Part 3: OSPF Adjacency & Neighbor Forming Proce…
This is the thrid article of our 6-part OSPF series (see below) that describes how OSPF routers perform neighbor relationship and adjacency. We’ll examine…
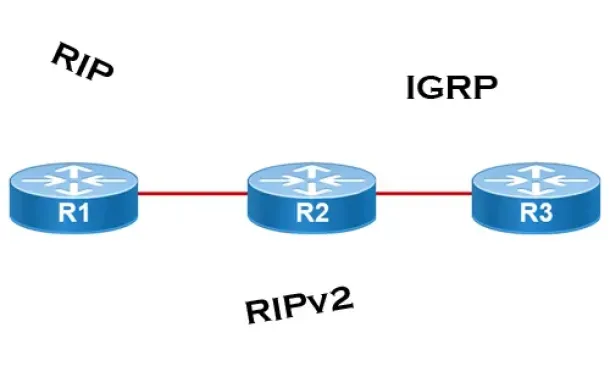
Routing
Distance Vector Routing Protocols
Distance Vector routing protocols use frequent broadcasts (255.255.255.255 or FF:FF:FF:FF) of their entire routing table every 30 sec. on all their interf…
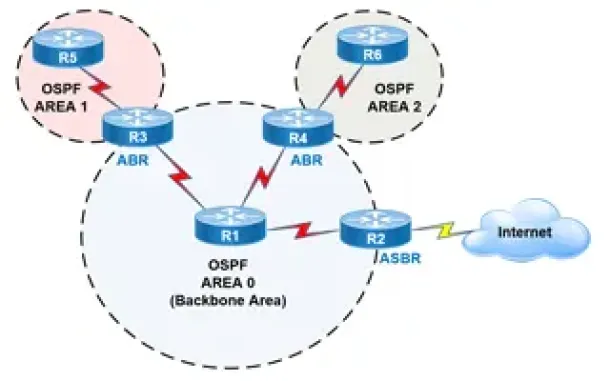
Routing
OSPF - Part 2: How OSPF Protocol Works & Basic Concept…
This article covers basic OSPF concepts and operation. We explain how OSPF works, how OSPF tables are built on an OSPF-enabled router and their purpose (N…
Windows Servers
Windows 2012 Server NIC Teaming – Load Balancing/Failo…
NIC Teaming, also known as Windows Load Balancing or Failover (LBFO), is an extremely useful feature supported by Windows Server 2012 that allows the aggr…
Cisco Routers
Cisco Router Basic ISDN Configuration
Configuration of ISDN interfaces on Cisco routers are usually considered a straight-forward process, however there are some details which can cause your I…
Windows Servers
Installing Active Directory Services & Domain Controll…
This article serves as an Active Directory tutorial covering installation and setup of Windows 2012 Active Directory Services Role & Domain Controller…
Cisco Routers
Configuring Cisco Dynamic Multipoint VPN (DMVPN) - Hub…
Our DMVPN Introduction article covered the DMVPN concept and deployment designs. We explained how DMVPN combines a number of technologies that give it its…
















