Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Are Cloud-Based Services Overhyped?
| Read |
|
Articles:
What if it Rains in the Cloud?
| Read |
| Read | |
| Read | |
|
Articles:
Email Security - Can't Live Without It!
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
Suggested Articles:

ManageEngine Firewall Analyzer
Challenges & Solutions to Managing Firewall Rul...
In today's interconnected digital landscape, where businesses rely heavily on networked systems and the internet for their operations, the importan...

OpManager - Network Monitoring & Management
Optimizing Cisco Router Performance: Best Pract...
Effective monitoring and management of Cisco routers and network devices are essential for ensuring a robust and efficient network infrastructure. ...

ManageEngine Firewall Analyzer
Dealing with Security Audit Challenges: Discove...
The utilization of log analyzers, such as Firewall Analyzer, in network infrastructure plays a pivotal role in enhancing cybersecurity and fortifyi...

EventLog Analyzer
Detecting Windows Server Security Threats with ...
Windows Servers stand as prime targets for hackers and malicious actors due to their widespread usage and historical vulnerabilities. These systems...
Featured Subcategories:
WireShark Articles:
Improve Network Analysis Efficiency with Colaso...
Troubleshooting network problems can be a very difficult and challenging task. While most IT engineers use a network analyzer to help solve network...
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing proce...
How to Detect Routing Loops and Physical Loops ...
When working with medium to large scale networks, IT departments are often faced dealing with network loops and broadcast storms that are caused by...
Introducing Colasoft Unified Performance Manage...
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, qua...
Your IP address:
3.21.33.186
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!

Palo Alto Networks
Configuring QoS on Palo Alto Firewalls: Class-based ...
This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and efficient ...
Palo Alto Networks
Palo Alto Firewall Configuration Options. Tap Mode, ...
Our previous article explained how Palo Alto Firewalls make use of Security Zones to process and enforce security policies. This article will explain th...
Palo Alto Networks
The Benefits of Palo Alto Networks Firewall Single P...
What makes Palo Alto Networks Next-Generation Firewall (NGFW) so different from its competitors is its Platform, Process and Architecture. Palo Alto Net...
Palo Alto Networks
Introduction to Palo Alto Next-Generation Network Fi...
During the past decade, we’ve seen the global IT security market flooded with new network security and firewall security appliances. New vendors emergin...
Windows Servers
How to Install Desktop Icons (Computer, User’s Files...
One of the first things IT Administrators and IT Managers notice after a fresh installation of Windows 2012 Server is that there are no Desktop Icons ap...
Windows Servers
Windows 2012 Server NIC Teaming – Load Balancing/Fai...
NIC Teaming, also known as Windows Load Balancing or Failover (LBFO), is an extremely useful feature supported by Windows Server 2012 that allows the ag...
Windows Servers
How to Enable ‘Web Server’ Certificate Template Opti...
In this article we will show you how to enable the ‘Web Server’ certificate template option on a Windows Certification Authority (Windows CA) Server.&nb...
Windows Servers
Troubleshooting Windows Server 2012 R2 Crashes. Anal...
There are umpteen reasons why your Windows Server 2012 R2 decides to present you with a Blue Screen of Death (BSOD) or the stop screen. As virtual machi...
Popular Topics
Windows Servers
Configuring Domain Group Policy for Windows 2003
Windows 2003 Group Policies allow the administrators to manage a group of people accessing a resource efficiently. The group policies can be used to con...
Network Protocol Analyzers
How to Detect SYN Flood Attacks with Capsa Network P...
This article explains how to detect a SYN Flood Attack using an advanced protocol analyser like Colasoft Capsa. We’ll show you how to identify and inspe...
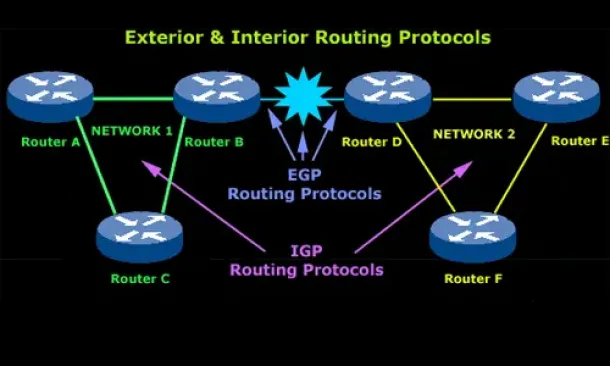
Routing
Introduction to Routing Protocols
Distance Vector, Link State RIP, IGRP, EIGRP, OSPF
Routing protocols were created for routers. These protocols have been designed to allow the exchan...
Windows Servers
Free Hyper-V eBook - Create, Manage and Troubleshoot...
With the introduction of Hyper-V on the Windows Server platform, virtualization has quickly become the de facto standard for all companies seeking to co...
Cisco Wireless
Configuring Cisco WLC Link Aggregation (LAG) with Po...
Cisco Wireless Controllers (WLC) support the configuration of Link Aggregation (IEEE 802.3ad - LAG) which bundles the controller ports into a single por...
Cisco Routers
How To Configure Router On A Stick - 802.1q Trunk To...
Router-on-a-stick is a term frequently used to describe a setup up that consists of a router and switch connected using one Ethernet link configured as ...
Cisco Services & Technologies
Fix Cisco VPN Client Break After Windows 10 Annivers...
Windows 10 latest update 1607 code named Anniversary update promises to introduce a number of significant enhancements including breaking your trustwort...
Cisco Switches
Resolving Cisco Switch & Router ‘DHCP Server Pool Ex...
In previous articles, we showed how it is possible to configure a Cisco router or Catalyst switch to provide DHCP server services to network clients. Ev...


















