Network Management Articles:

ManageEngine Firewall Analyzer
Discover the Ultimate Firewall Management Tool:...
Firewall security management is a combination of monitoring, configuring, and managing your firewall to make sure it runs at its best to effectively ward off network security threats. In this artic...

Netflow
NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows while at the same time analyze traffic patterns, ...
Netflow
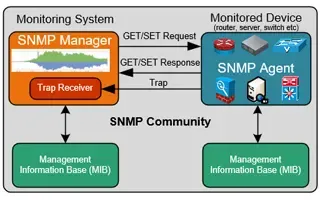
Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the network and in some cases discern the cause of net...

ManageEngine Firewall Analyzer
Ensuring Compliance and Business Continuity in ...
In the wake of digital transformation, the work landscape as we know it has undergone a dynamic shift. People can now work from home, from the office, or anywhere with a stable internet connection....
Featured Subcategories:
Network Protocol Analyzer Articles:
Network Protocol Analyzers
How to Detect Routing Loops and Physical Loops ...
When working with medium to large scale networks, IT departments are often faced dealing with network loops and broadcast storms that are caused by user error, faulty network devices or incorrect c...
Network Protocol Analyzers
How To Detect ARP Attacks & ARP Flooding With C...
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC address and responding on their behalf, while at the s...
Network Protocol Analyzers
How to Reconstruct HTTP Packets/Data & Monitor ...
HTTP reconstruction is an advanced network security feature offered by nChronos version 4.3.0 and later. nChronos is a Network Forensic Analysis application that captures packets/data around the cl...
Network Protocol Analyzers
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing processes that not only consumes valuable bandwidth, bu...
Virtualization & VM Backup:
Virtualization & VM Backup
6 Key Areas to Consider When Selecting a VM Bac...
Backup and Disaster recovery are core considerations for any business with an IT footprint, whether that is on-premises or in the cloud.
Your business depends on reliable IT systems to support the...
Virtualization & VM Backup
How to Enable or Disable SSH on VMware ESXi via...
SSH access to VMware’s ESXi server is by disabled by default however there are many reasons where SSH might be required. VMware and System administrators often find the need to perform advanced adm...
Virtualization & VM Backup
World Backup Day with Free Amazon Voucher and P...
Celebrate World Backup Day and WIN with Altaro!
We all remember how grateful we were to have backup software when facing so many data loss mishaps and near-catastrophes.
If you manage your com...

Virtualization & VM Backup
8 Critical Features to Have in a VM Backup Solu...
Businesses that rely on virtual machines for their day-to-day operations should think twice about securing their infrastructure. Modern use of virtual machines stems from the benefits of virtualiza...
Firewall Articles:
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial...
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Firewall appliances and technical specifications, ...
Palo Alto Networks
Complete Guide: Configuring IPSec VPN between P...
This article will show you how to configure an IPSec VPN tunnel between a Palo Alto firewall (all PANOS versions) and Meraki MX security appliance. Our comprehensive guide includes IPSec VPN setup ...
Cisco Firewalls
Demystifying Cisco AnyConnect 4.x Licensing. Pl...
In late 2014, Cisco announced the new licensing model for the latest AnyConnect Secure Mobility client v4.x. With this new version, Cisco introduced a number of new features, but also simplified th...
Cisco Firewalls
Understand & Configure NAT Reflection, NAT Loop...
This article examines the concept of NAT Reflection, also known as NAT Loopback or Hairpinning, and shows how to configure a Cisco ASA Firewall running ASA version 8.2 and earlier plus ASA version ...
Your IP address:
3.141.31.240
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Top Picks
Windows Servers
Windows Server 2016 VM Backup with Altaro's New VM Backup with Augmented Inline Deduplication
Altaro has released Altaro VM Backup, a faster and lighter upgrade to its flagship Hyper-V and VMware backup solution, which now supports all Windo...

Palo Alto Networks
Configuring QoS on Palo Alto Firewalls: Class-based Policies, QoS Profiles, Enabling QoS on Firewall Interfaces
This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and effic...
Cisco Routers
How and Why You Should Verify IOS Images On Cisco Routers & Catalyst Switches. Identify Corrupt & Tampered Images using SHA2 or MD5 Verification
Chances are we’ve all needed to upgrade our Cisco’s device IOS software at some point. While upgrading the IOS software on a Cisco device is consid...
VPN Services & Guides
Best VPN Review: Private Internet Access (PIA) Features, Pricing, User Experience, Benchmarking & Torrenting
The market for Virtual Private Networks has exploded over the past few years. A wealth of new providers has appeared, promising logless browsing, t...




















